30 Tage kostenlos
Funktionsvergleich
| Standard | Premium | |
| Protect against data loss proactively | ||
| Feature | Standard | Premium |
| Enforced single sign-on (SSO) ? | Standard ✓ | Premium ✓ |
| SCIM automated user provisioning ? | Standard ✓ | Premium ✓ |
| Authentication policies ? | Standard ✓ | Premium ✓ |
| External user security ? | Standard ✓ | Premium ✓ |
| Enforced two-step verification ? | Standard ✓ | Premium ✓ |
| Mobile app management (MAM) ? | Standard ✓ | Premium ✓ |
| API token controls ? | Standard ✓ | Premium ✓ |
| Data security policies ? | Standard ✓ | Premium ✓ |
| Data classification ? | Standard - | Premium ✓ |
| Enforce data security policies by classification ? | Standard - | Premium ✓ |
| Detect and investigate suspicious activity | ||
| Feature | Standard | Premium |
| Automatic product discovery ? | Standard ✓ | Premium ✓ |
| Organization insights ? | Standard ✓ | Premium ✓ |
| Organization audit log: Admin activity ? | Standard ✓ | Premium ✓ |
| Comprehensive organization audit log: User activity, API tokens, Webhooks ? | Standard - | Premium ✓ |
| Anomalous activity detections ? | Standard - | Premium ✓ |
| Content scanning ? | Standard - | Premium ✓ |
| SIEM integrations ? | Standard - | Premium ✓ |
| Alert messaging integrations ? | Standard - | Premium ✓ |
| Respond to threats before they become incidents | ||
| Feature | Standard | Premium |
| Alert investigations ? | Standard - | Premium ✓ |
| Actor profiles ? | Standard - | Premium ✓ |
| Remediation recommendations ? | Standard - | Premium ✓ |
| Remediation workflows ? | Standard - | Premium ✓ |
| Alert hand-off ? | Standard - | Premium ✓ |
See Atlassian Guard in action
Funktionen von Atlassian Access
| Setze für alle verwalteten Benutzer Single-Sign-On (SSO) durch, damit sie sich bei den Atlassian Cloud-Produkten über die in deinem Unternehmen vorhandenen Identitätsanbieter authentifizieren können. Dies bedeutet, sie können auf mehrere Tools mit denselben Zugangsdaten zugreifen und gleichzeitig eine sicherere Authentifizierungsmethode als die einfache Anmeldung mit Benutzernamen und Passwort verwenden. |
| Automatisiere die Lebenszyklusverwaltung von Benutzern mit der Bereitstellung und Aufhebung der Bereitstellung von Benutzern per SCIM. Der Zugriff auf die Atlassian Cloud-Produkte wird durch Regeln in deinem externen Verzeichnis definiert. Die Benutzerbereitstellung reduziert den manuellen Aufwand, wenn neue Mitarbeiter oder Teammitglieder Zugriff auf Anwendungen erhalten sollen. |
| Administratoren können Authentifizierungsrichtlinien einrichten, um Sitzungsdauer, Single-Sign-On (SSO), Passwortrichtlinien und Zwei-Faktor-Authentifizierung zu verwalten. Es können mehrere Richtlinien erstellt und auf verschiedene Untergruppen von verwalteten Konten angewendet werden. |
| Die verpflichtende Zwei-Faktor-Authentifizierung kann als Teil einer Authentifizierungsrichtlinie angewendet werden. Dazu müssen die Benutzer in einer Organisation die Zwei-Faktor-Authentifizierung aktivieren, um sich einloggen und auf die Atlassian Cloud-Produkte zugreifen zu können. |
| Erstelle und verwalte mit der mobilen Anwendungsverwaltung (Mobile Application Management, MAM) Sicherheitsrichtlinien, die sowohl auf verwaltete als auch auf nicht verwaltete Benutzer angewendet werden können. Richtlinien können auf Organisationsebene oder für ausgewählte Benutzer festgelegt werden, um zusätzliche Sicherheitskontrollen wie die Deaktivierung von Screenshots, Datenexportbeschränkungen und Anforderungen an die Geräteverschlüsselung bereitzustellen. |
| Verschaffe dir Einblick in die Schatten-IT, indem du ermittelst, wann verwaltete Benutzer in deinem Unternehmen Instanzen für Atlassian Cloud-Produkte erstellen. Die automatische Produkterkennung identifiziert den Produktadministrator und die Anzahl der Benutzer, die diese Produkte verwenden. |
| Umfangreiche Protokolle zu Admin-Aktivitäten werden in deiner Atlassian Cloud-Organisation angezeigt. Ein Audit-Protokoll der Organisation zeigt Administratoren, wer wann welche Administratoraktivitäten ausgeführt hat, damit jedes verdächtige Verhalten nachverfolgt und identifiziert werden kann. |
| Integriere Atlassian Access in deinen CASB, um eine vollständige Aufzeichnung der Anmeldungs- und Verwaltungsaktivitäten in Atlassian zu erfassen. Verteidige dich gegen allgemeine Bedrohungen wie kompromittierte Benutzeranmeldedaten, schlechte Passworthygiene oder Insiderbedrohungen durch überprivilegierte Konten. Erfahre mehr darüber, wie du deine McAfee MVISION- oder Microsoft Defender-CASBs verbindest. |
Enforced single sign-on (SSO)
Hinweis: Der Einfachheit halber listet diese Tabelle nur bis zu 5.000 Benutzer auf. Bei Access gibt es keine Benutzergrenzen. Rechne Jahrespreise für über 5.000 Benutzer bitte mithilfe des Preisrechners aus.
SCIM automated user provisioning
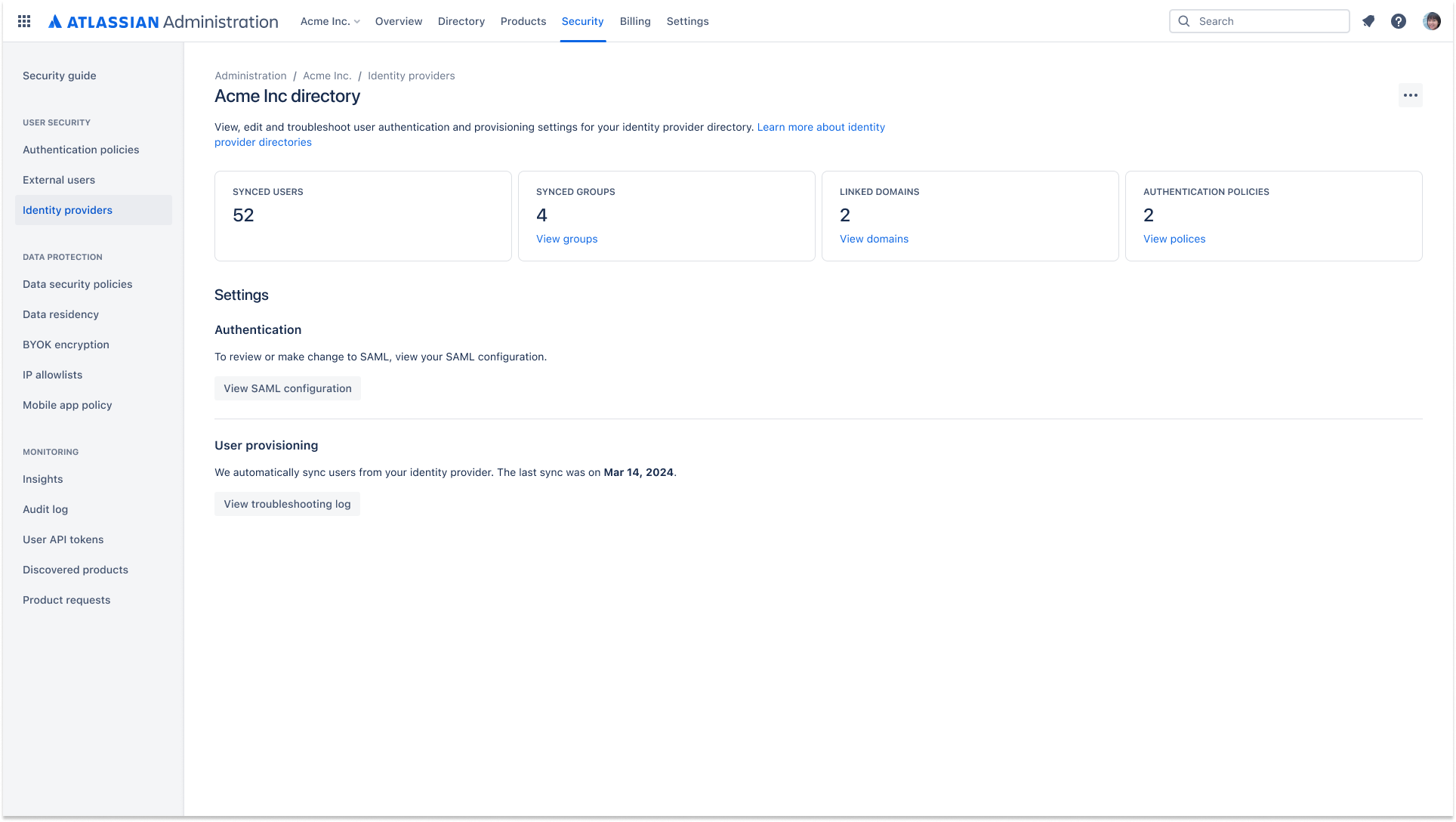
Automate user lifecycle management with SCIM provisioning and de-provisioning. Access to Atlassian cloud products will be defined by rules set in your external directory.
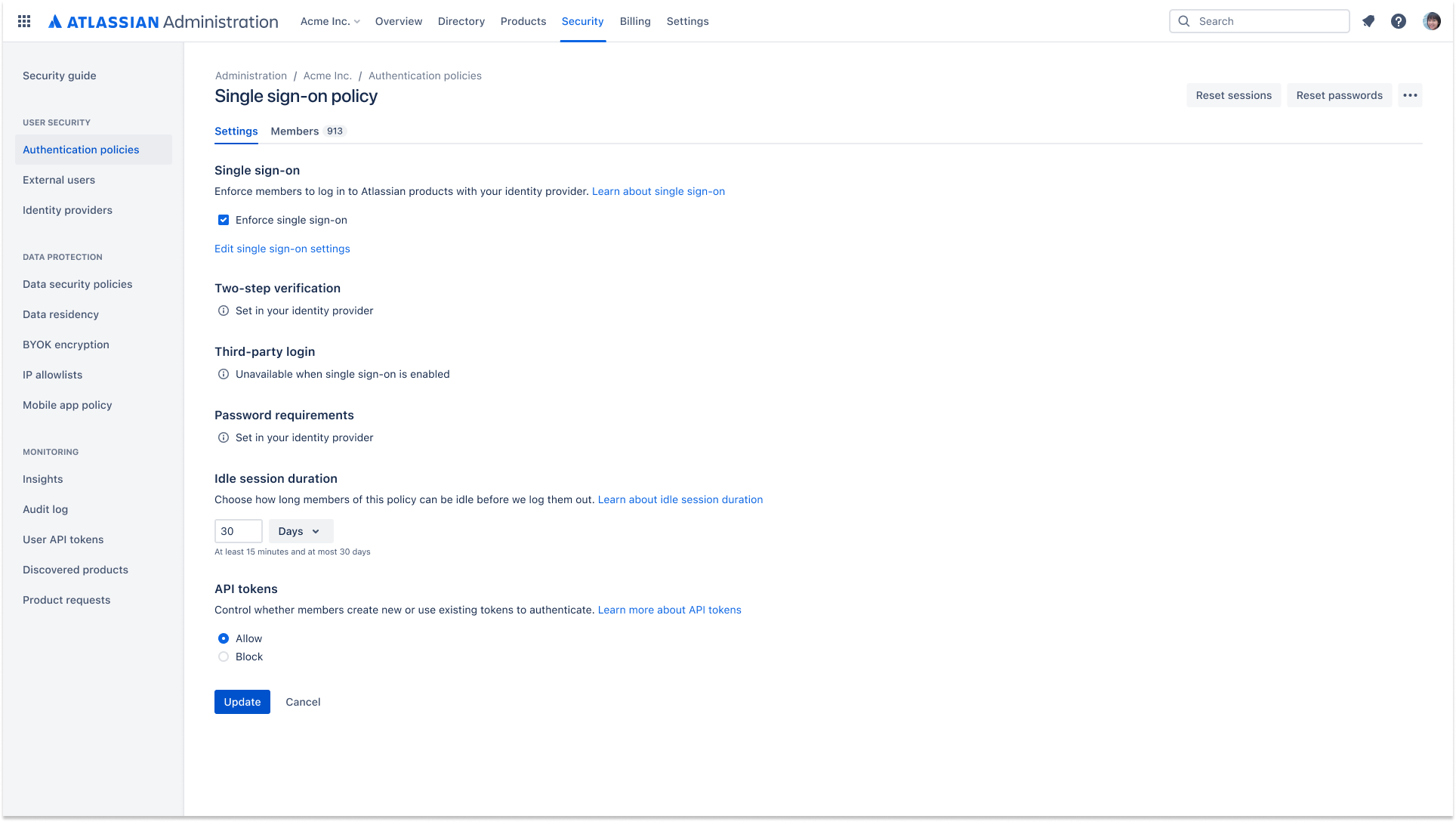
Authentication policies
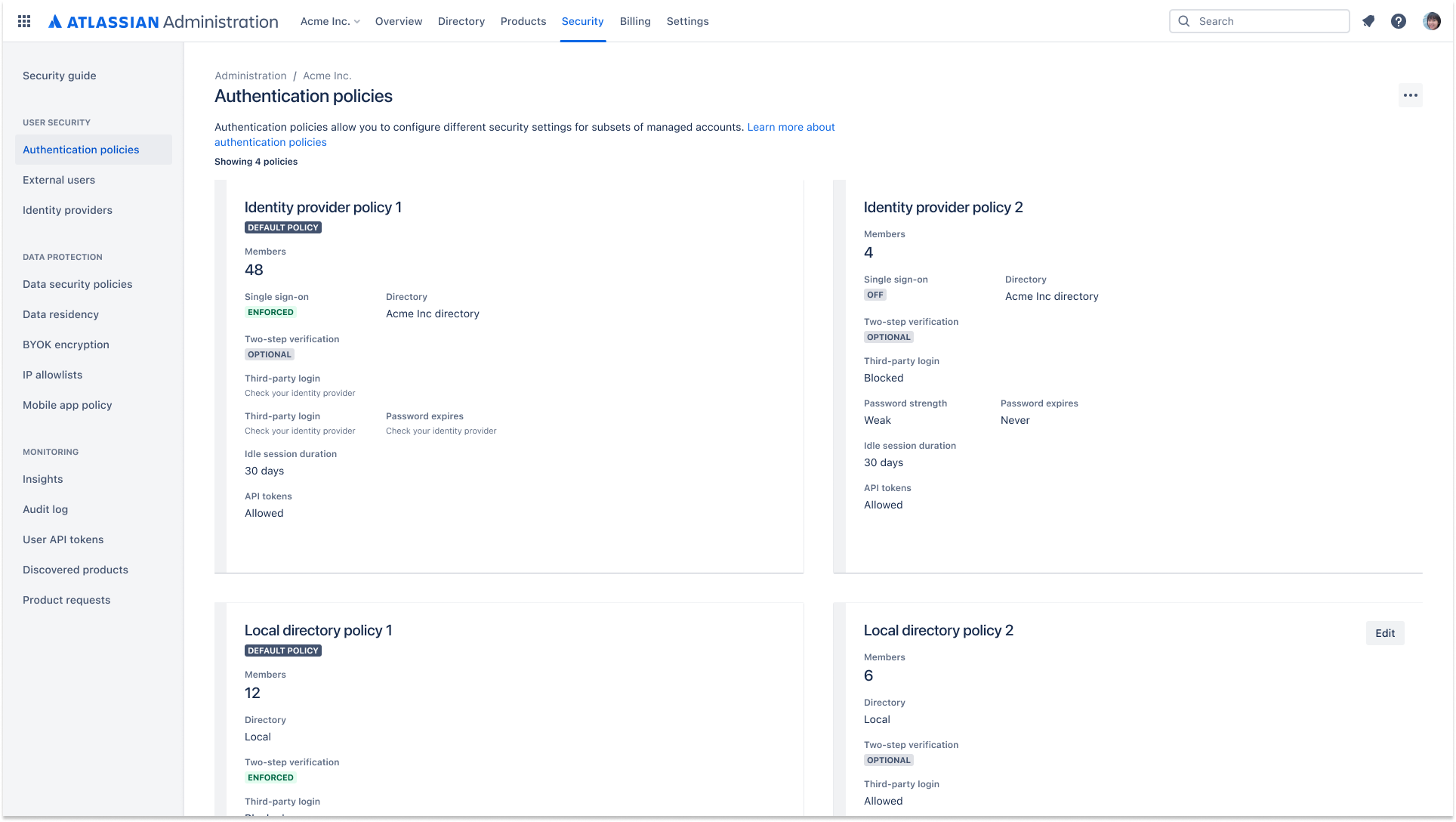
Admins can set authentication policies to manage session duration, single sign-on (SSO), password policies, and two-step verification. Multiple policies can be created and applied to different subsets of managed accounts.
External user security
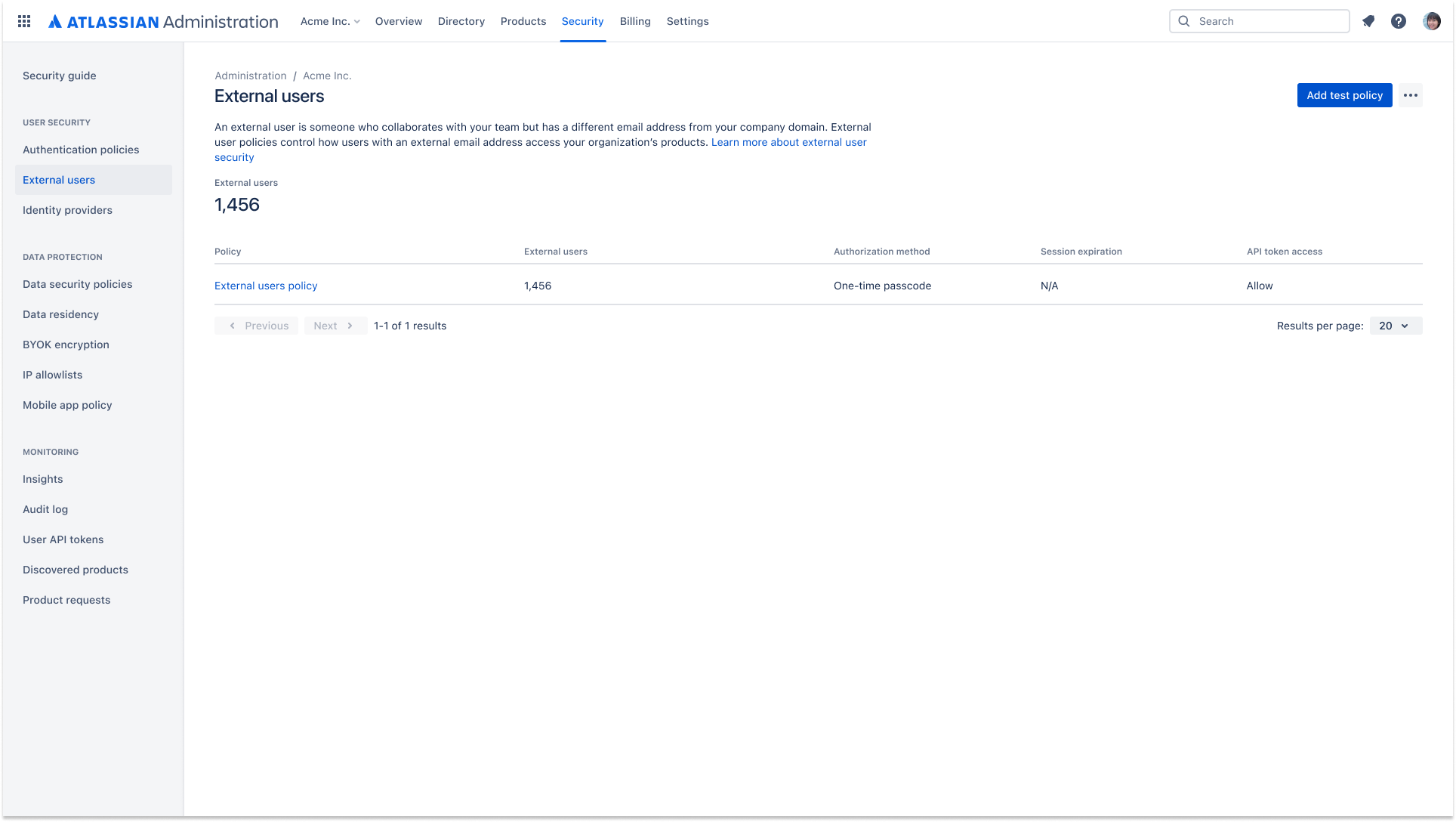
An external user policy allows you to apply security settings, including two-step verification, to external users. The settings apply to all the external users in your Atlassian organization.
Mobile app management (MAM)
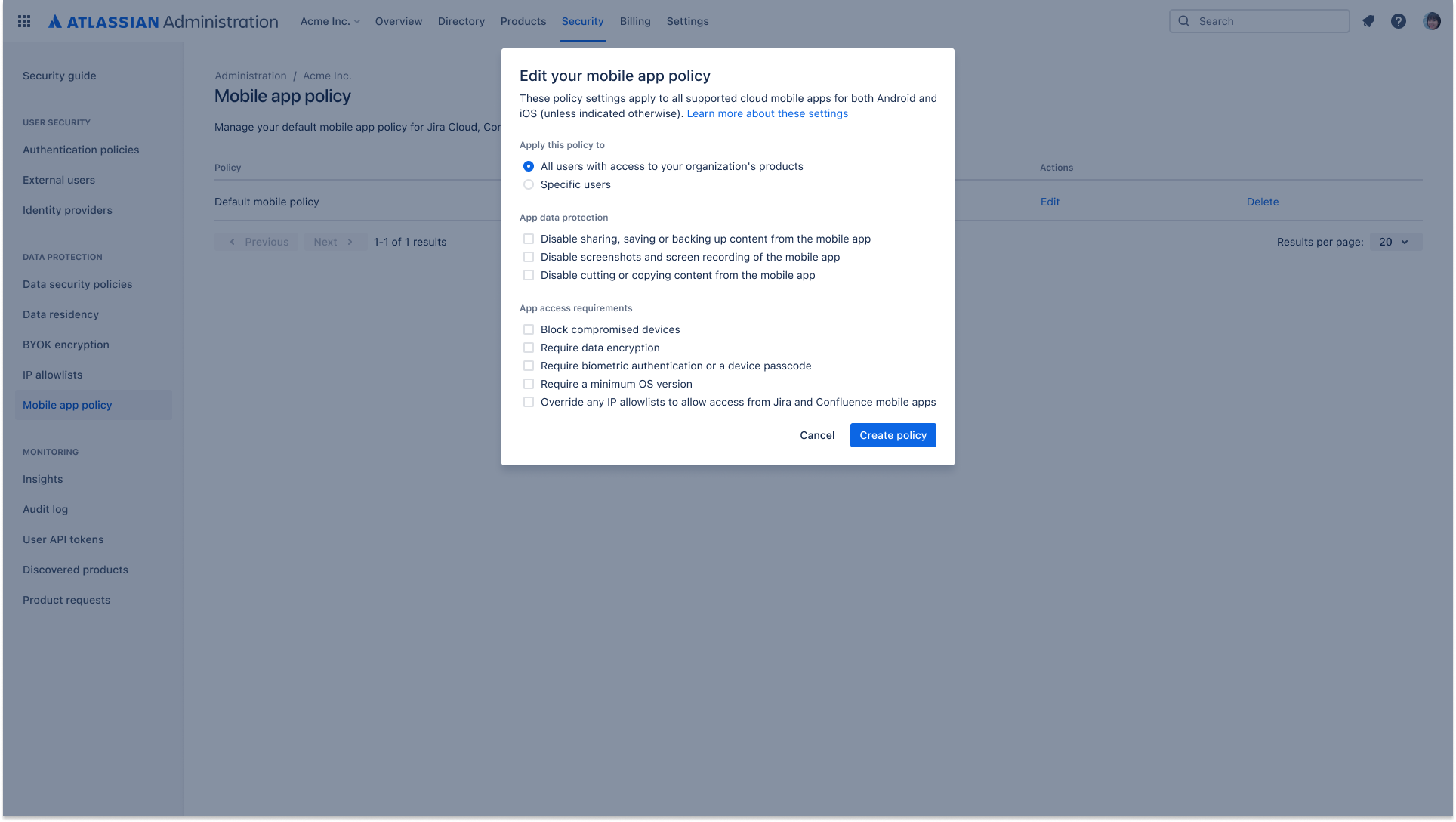
Create and manage security policies that can be applied to both managed and unmanaged users with mobile app management (MAM). Policies can be set at the organization level, or designated for select users to provide additional security controls such as screenshot disabling, data export restrictions and device encryption requirements
API token controls
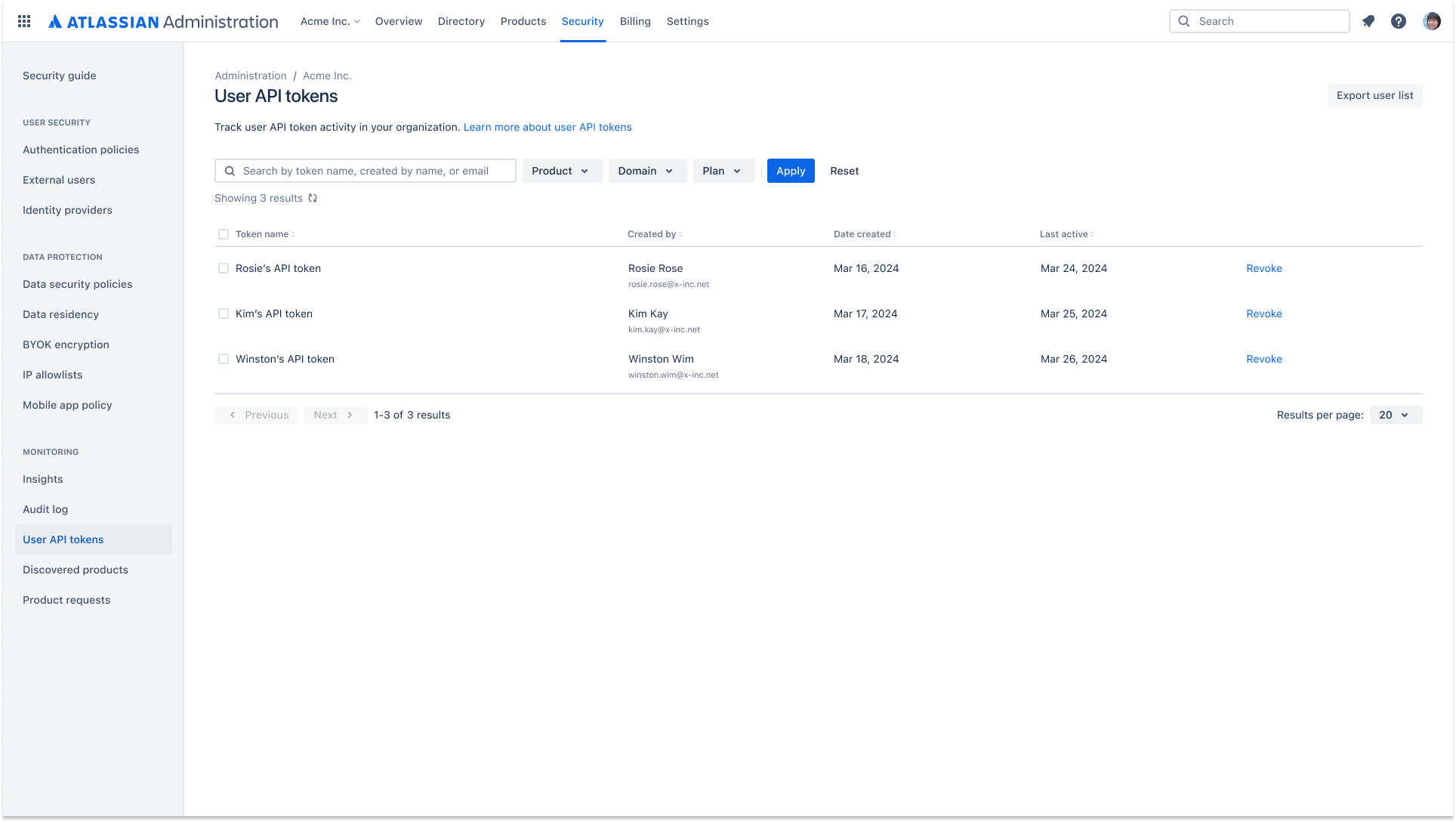
Admins have greater visibility and control over API token management and its lifecycle. This includes controlling which users can create an API token to access data and viewing which users are creating and revoking API tokens.
Data security policies
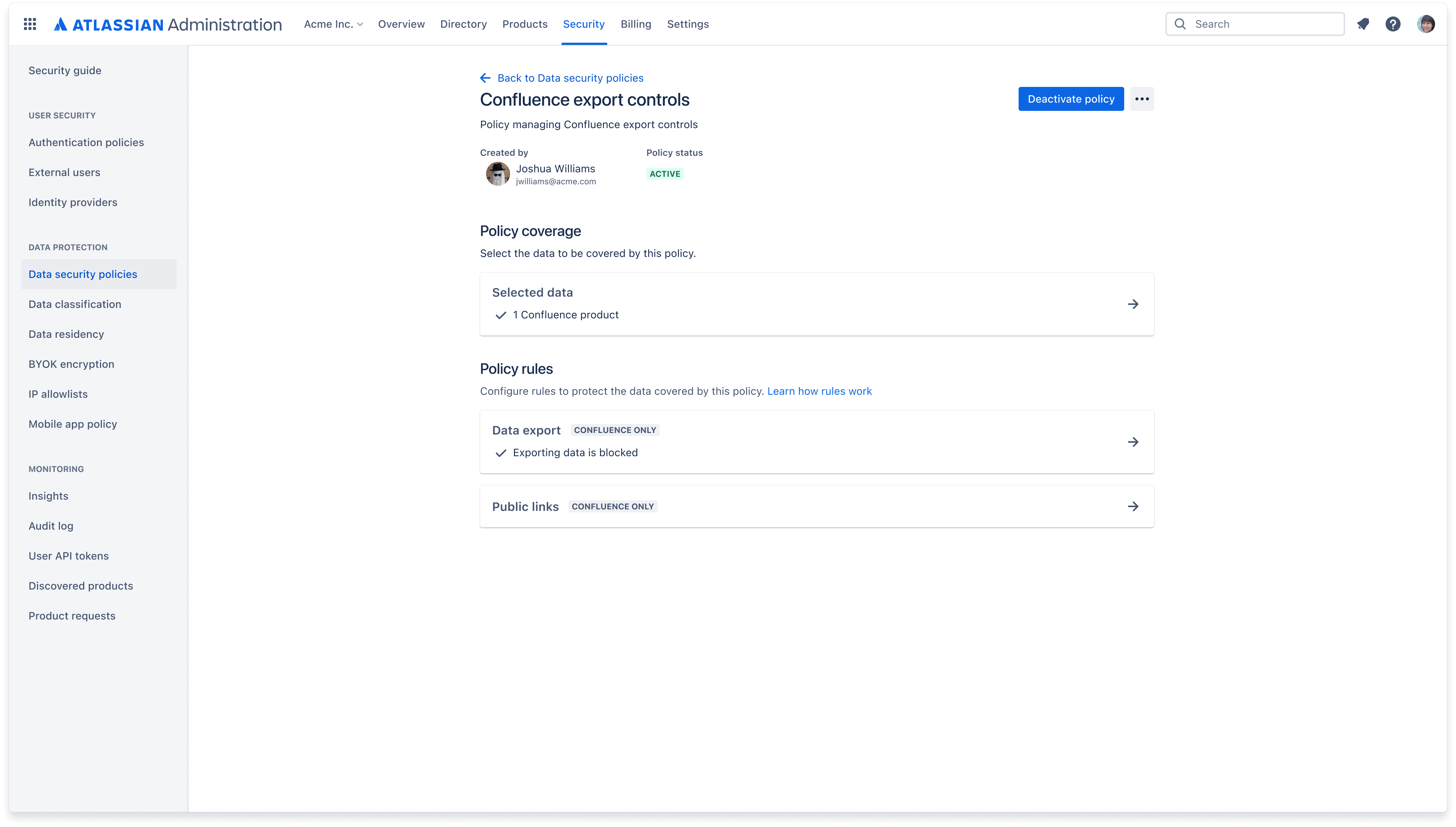
A data security policy helps you keep your organization’s data secure. Create policies to govern how users, apps, and people outside of your organization can interact with content such as Confluence pages and Jira issues.
Data classification
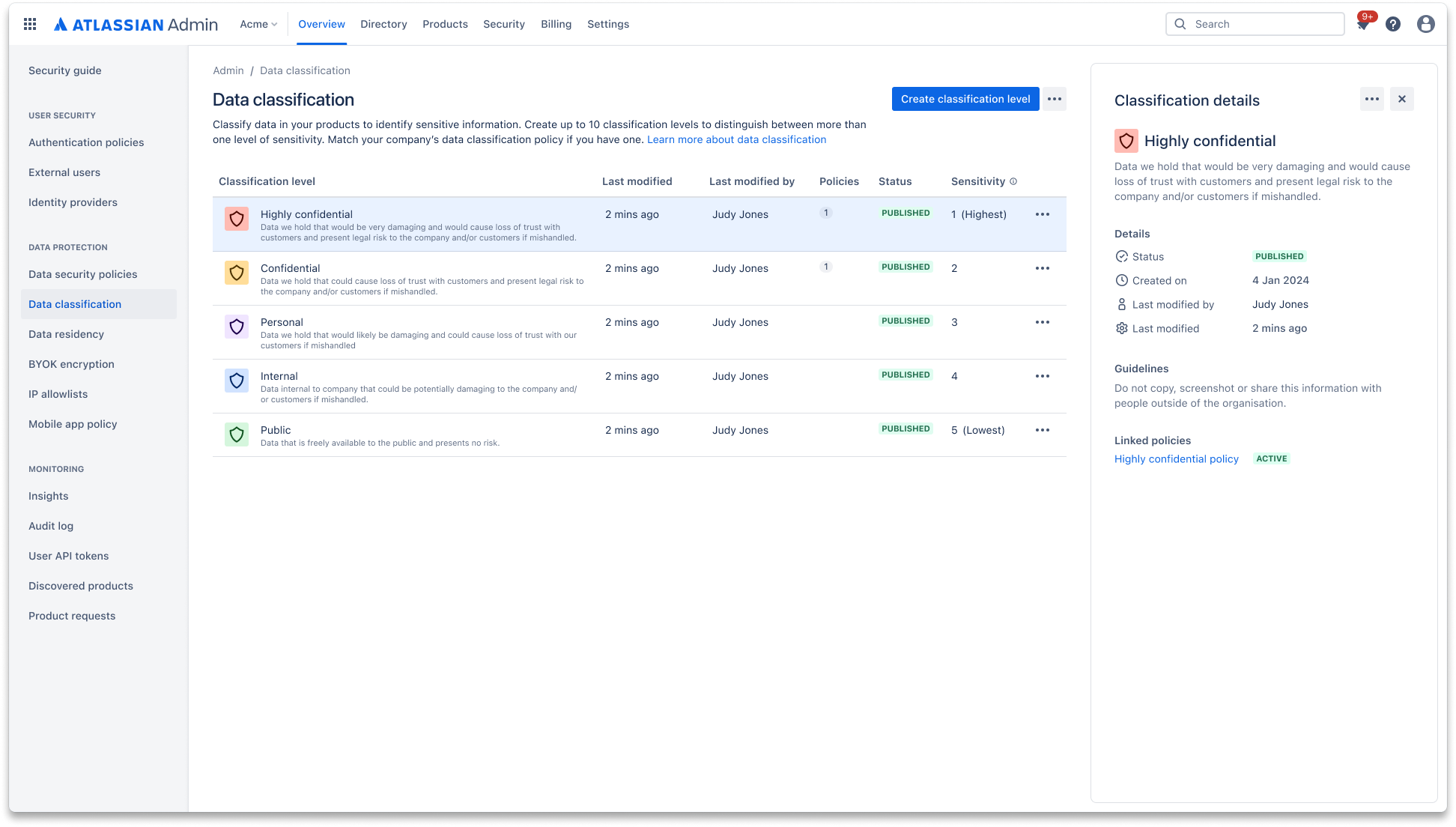
Data classification allows admins to define their data governance approach and label critical data accordingly within Atlassian products. Admins can set data security policies and rules to control user interaction based on data classification level.
Enforce data security policies by classification
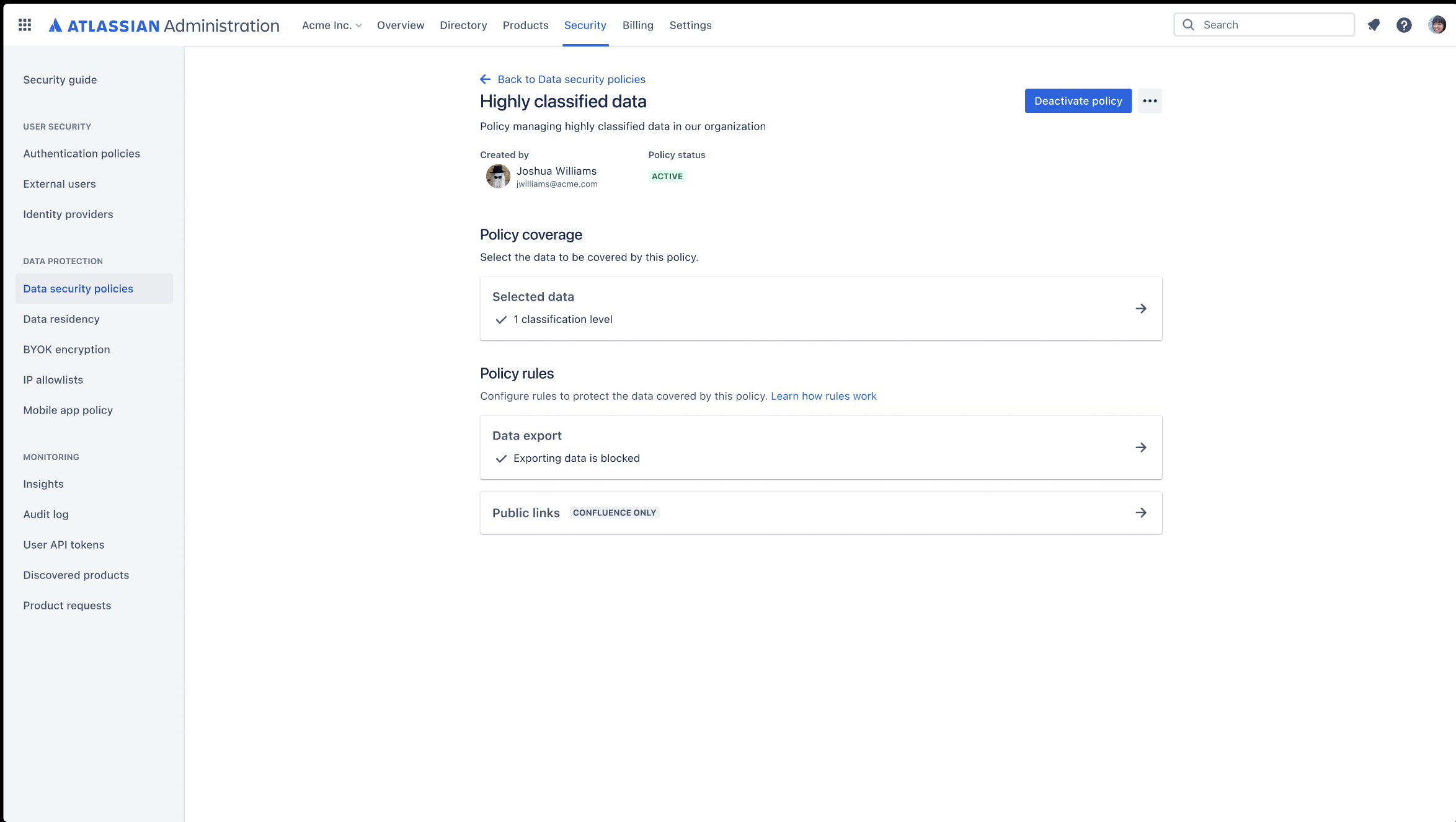
Use data classification levels as a coverage in your data security policy. Create policies to govern how users, apps, and people outside of your organization can interact with content such as Confluence pages and Jira issues.
Use data classification to set additional rules within your data security policy, including: "Block Export" rule in Confluence and Jira, “Anonymous Access” rule in Jira, and “Block Public Links” rule in Confluence using classification.
Automatic product discovery
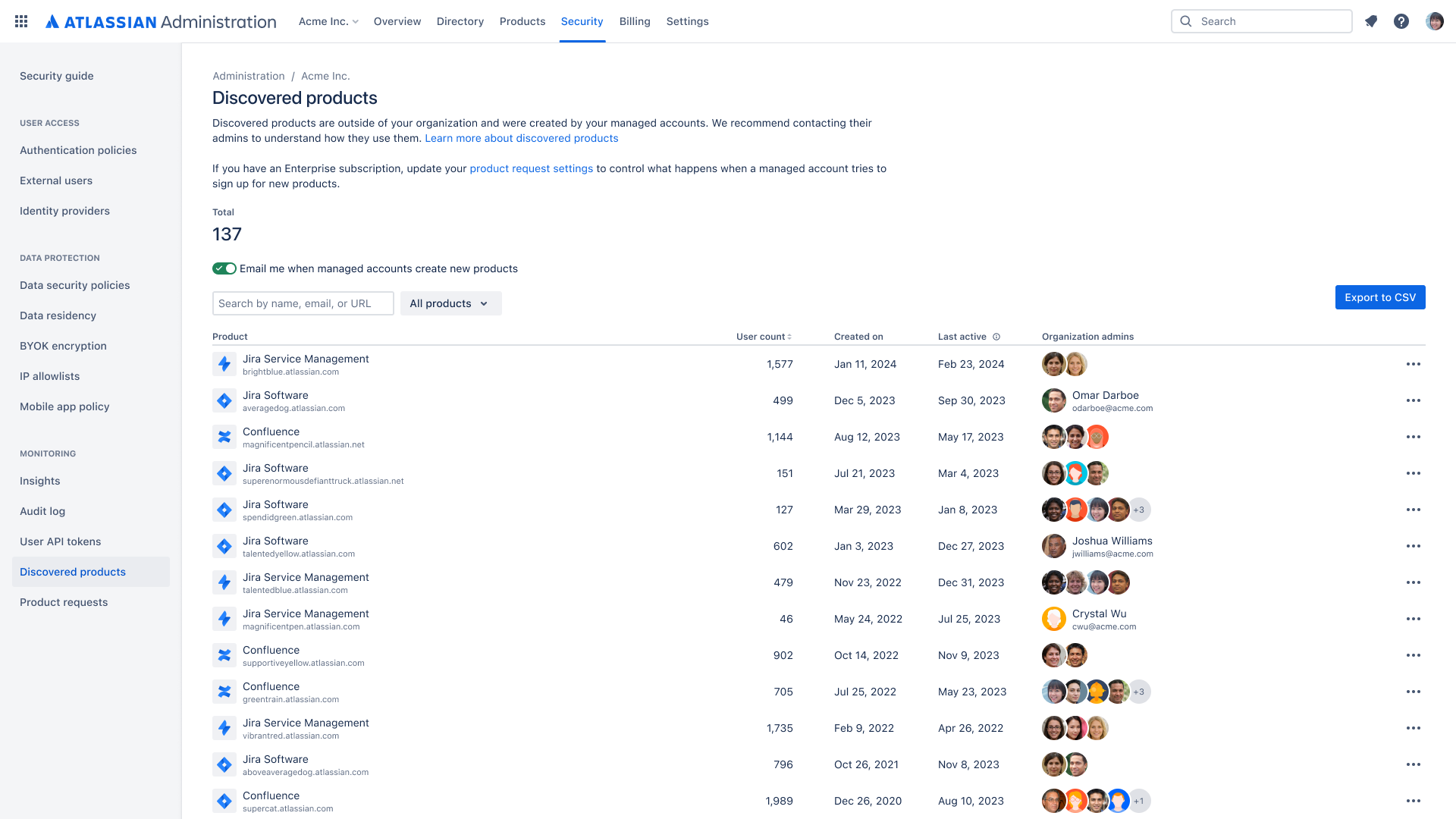
Gain visibility into shadow IT by discovering when managed users in your organization create instances across Atlassian cloud products. Automatic product discovery identifies the product administrator and how many users are using these products.
Organization insights
Admins can achieve better visibility into the usage of their Atlassian products and make more data-driven decisions when it comes to increasing adoption or optimizing their products' ROI.
Organization audit log: Admin activity
79b0.png)
A centralized log of admin activity across your Atlassian cloud organization. Gain a full view of the who, what, and when of admin activity to help track and identify any suspicious behavior. Using APIs, integrate with your third party tools, such as a CASB.
Comprehensive organization audit log: User activity, API tokens, Webhooks
79b0.png)
A comprehensive log of org admin, product admin, and user activity that takes place in the Atlassian cloud organization. This provides organization admins with visibility into activities like which managed users have created an API token or what organizational resources are being accessed by managed and external users via API tokens. Audit log webhooks are customized HTTP callbacks that trigger in response to audit log events.
Anomalous activity detections
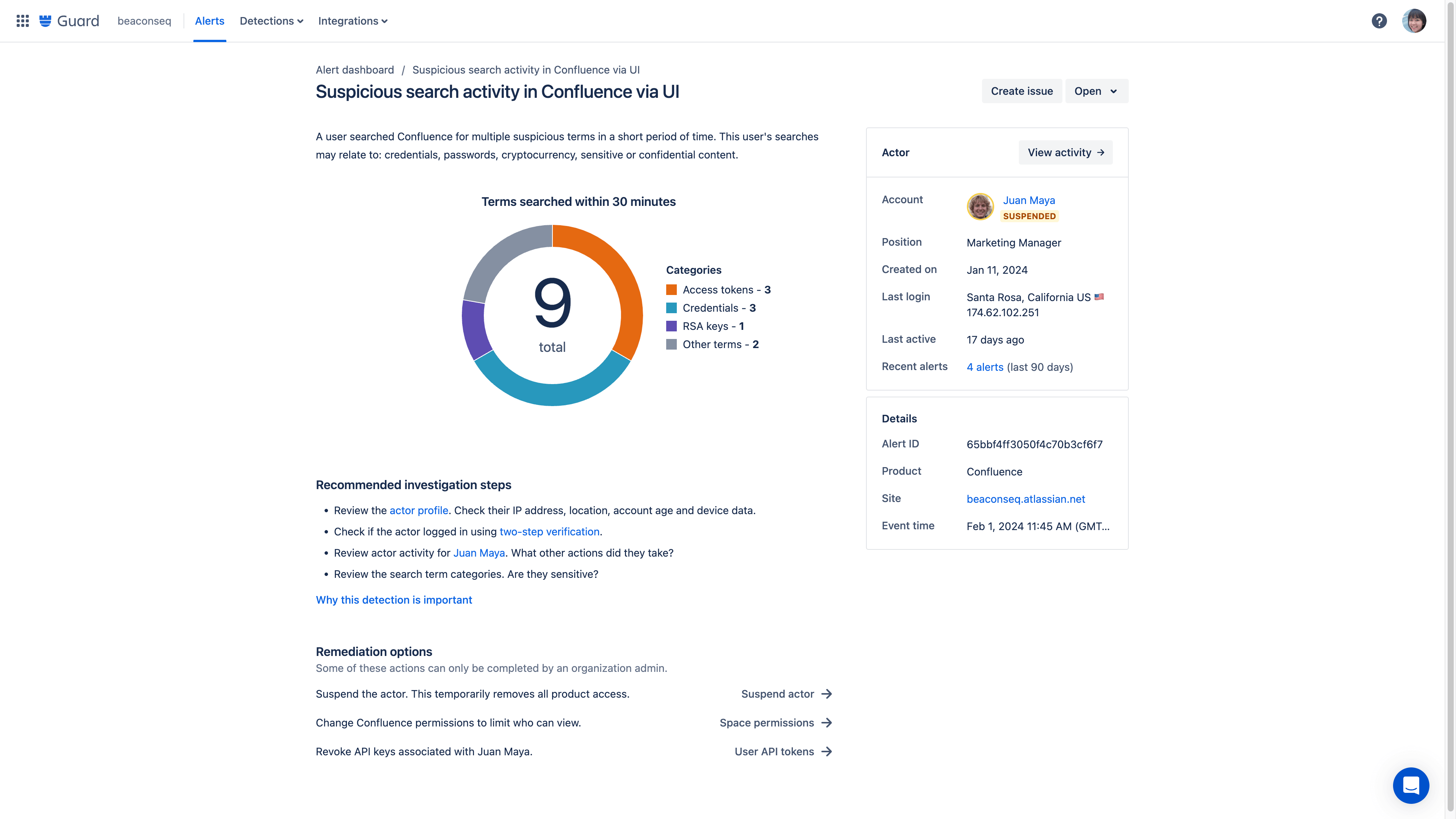
Anomalous activity detections provide intelligent oversight across your Atlassian cloud products by analyzing user activity and notifying you of potential risks. These queries search activity logs and alert you to any potentially concerning activity that requires review.
Content scanning
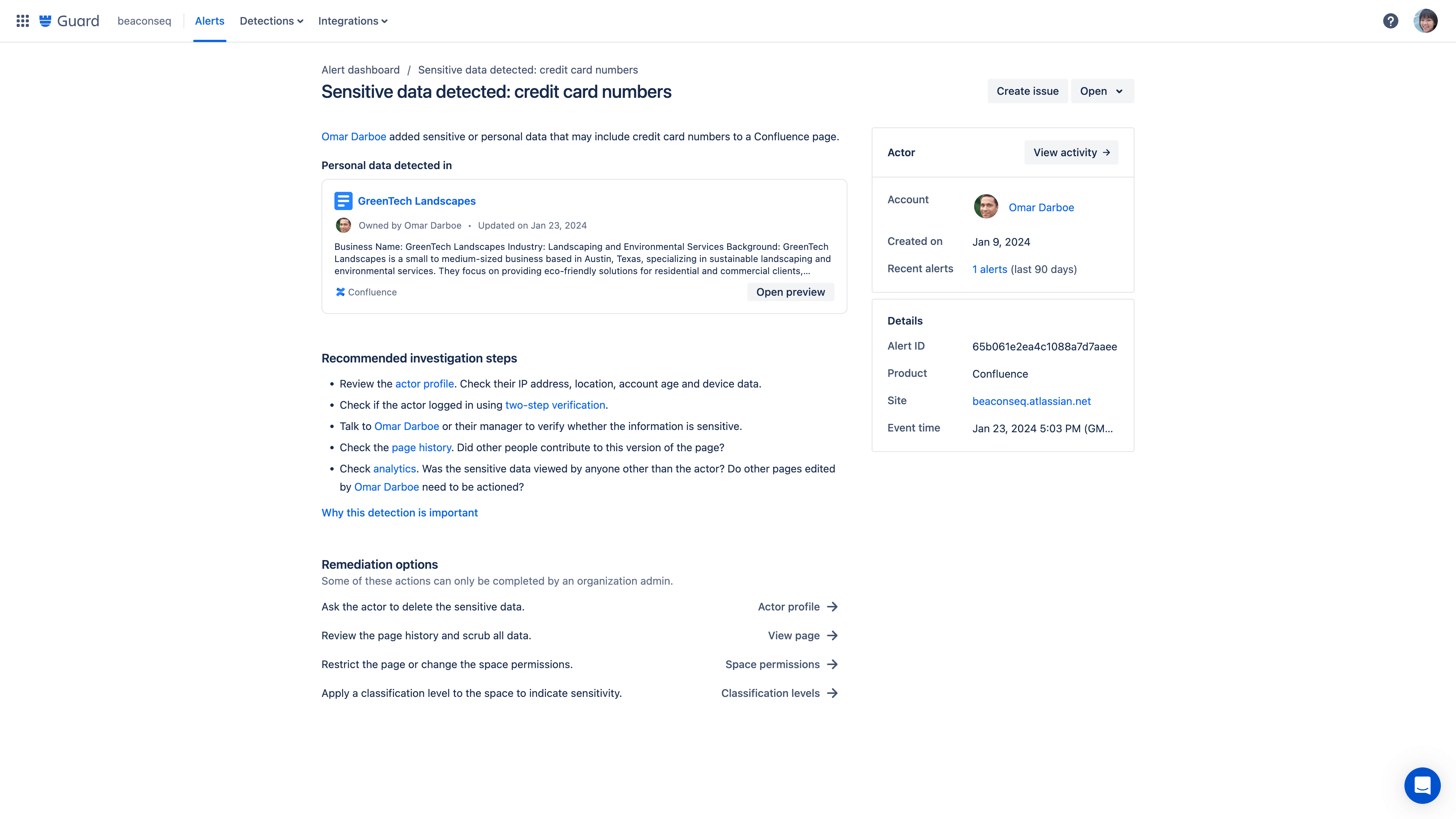
Content scanning detection rules monitor for critical data being added to Confluence pages. These detections generate alerts for any potentially concerning content that requires review.
SIEM integrations
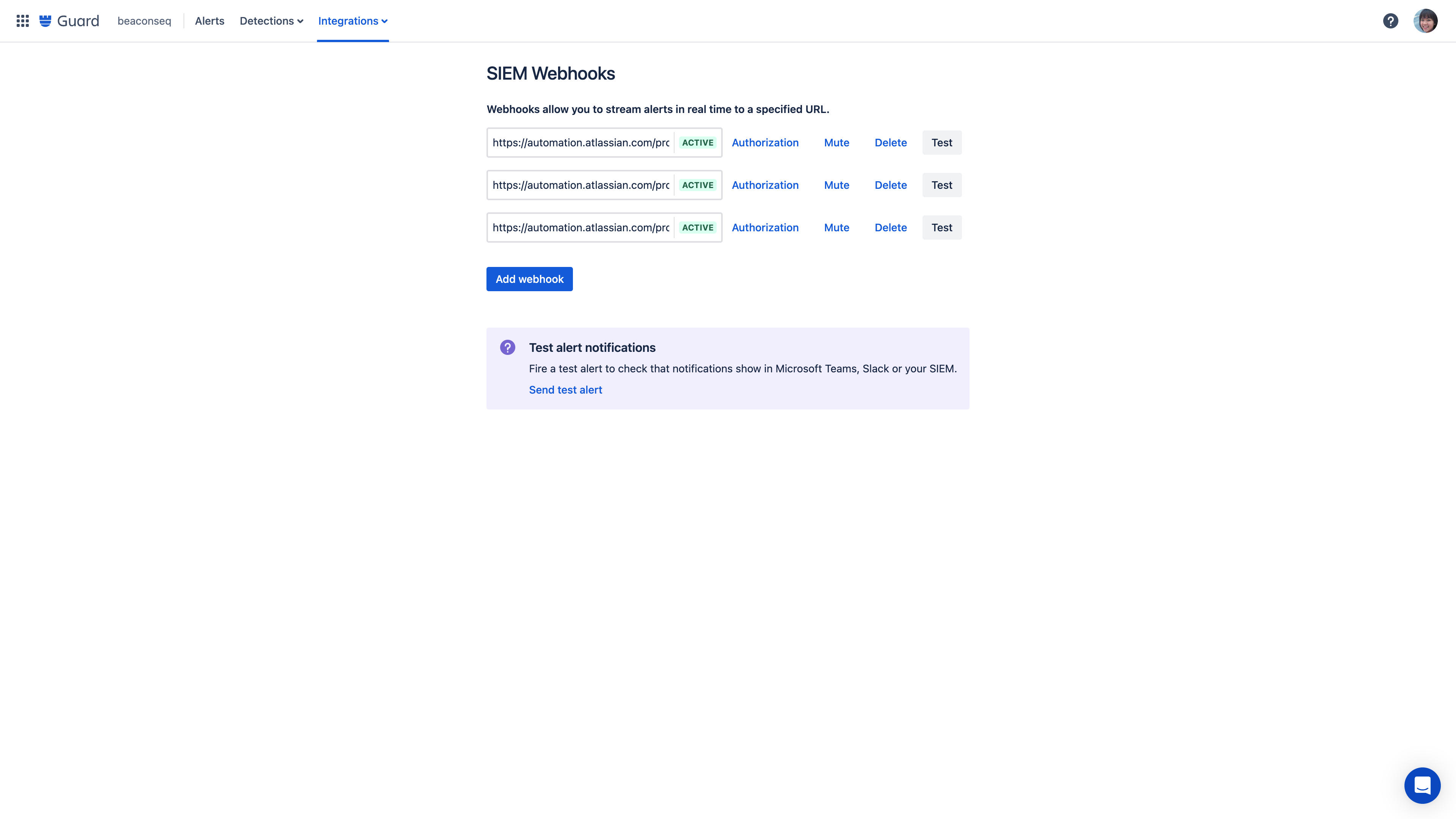
Using webhooks, send alerts about anomalous activity to any destination, including your organization-wide SIEM or an automation tool like Jira Automation, Zapier, or Workato.
Alert messaging integrations
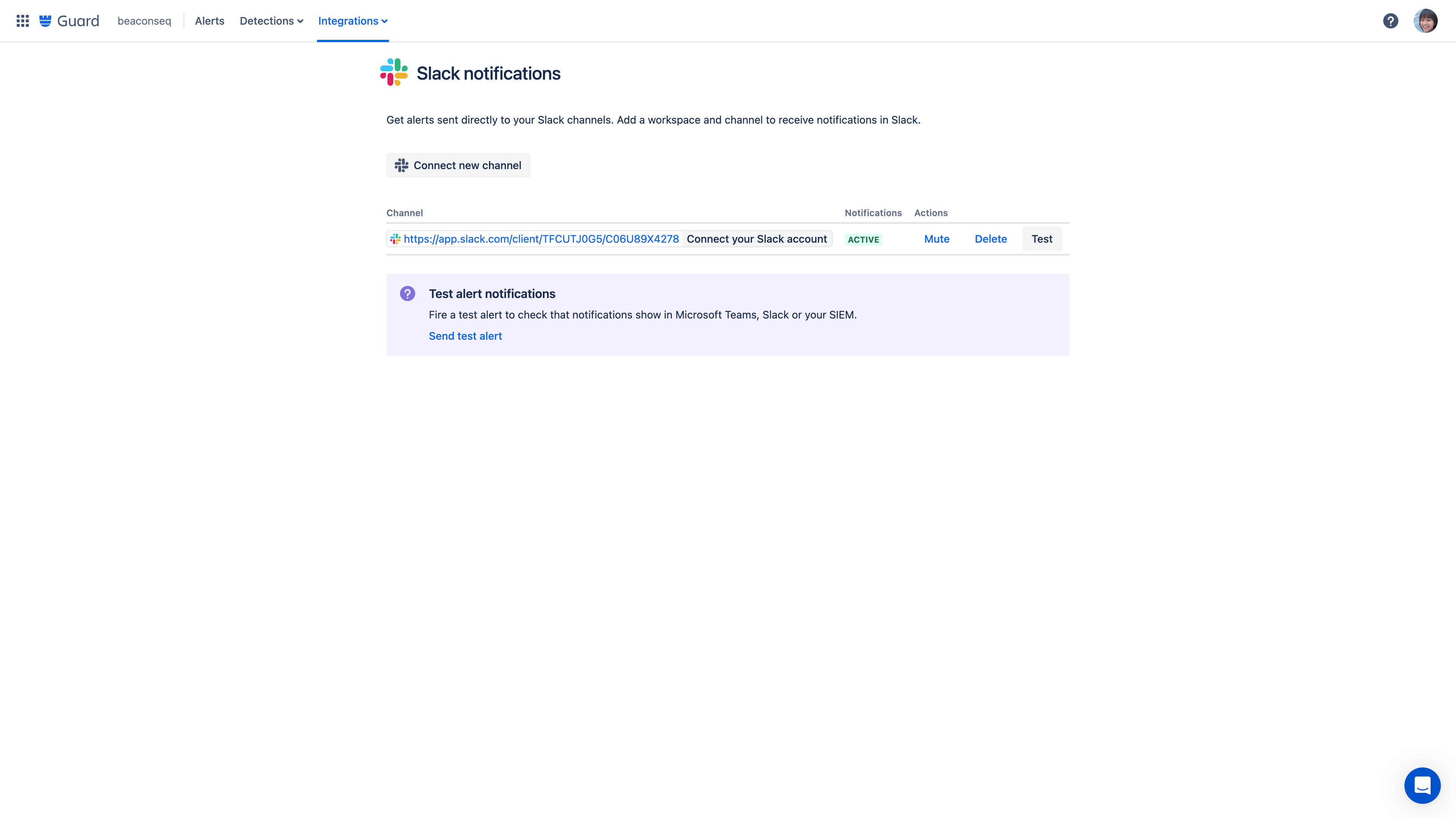
Integrate alert messages to your organization-wide tools like Slack, Microsoft Teams, and more.
Alert investigations
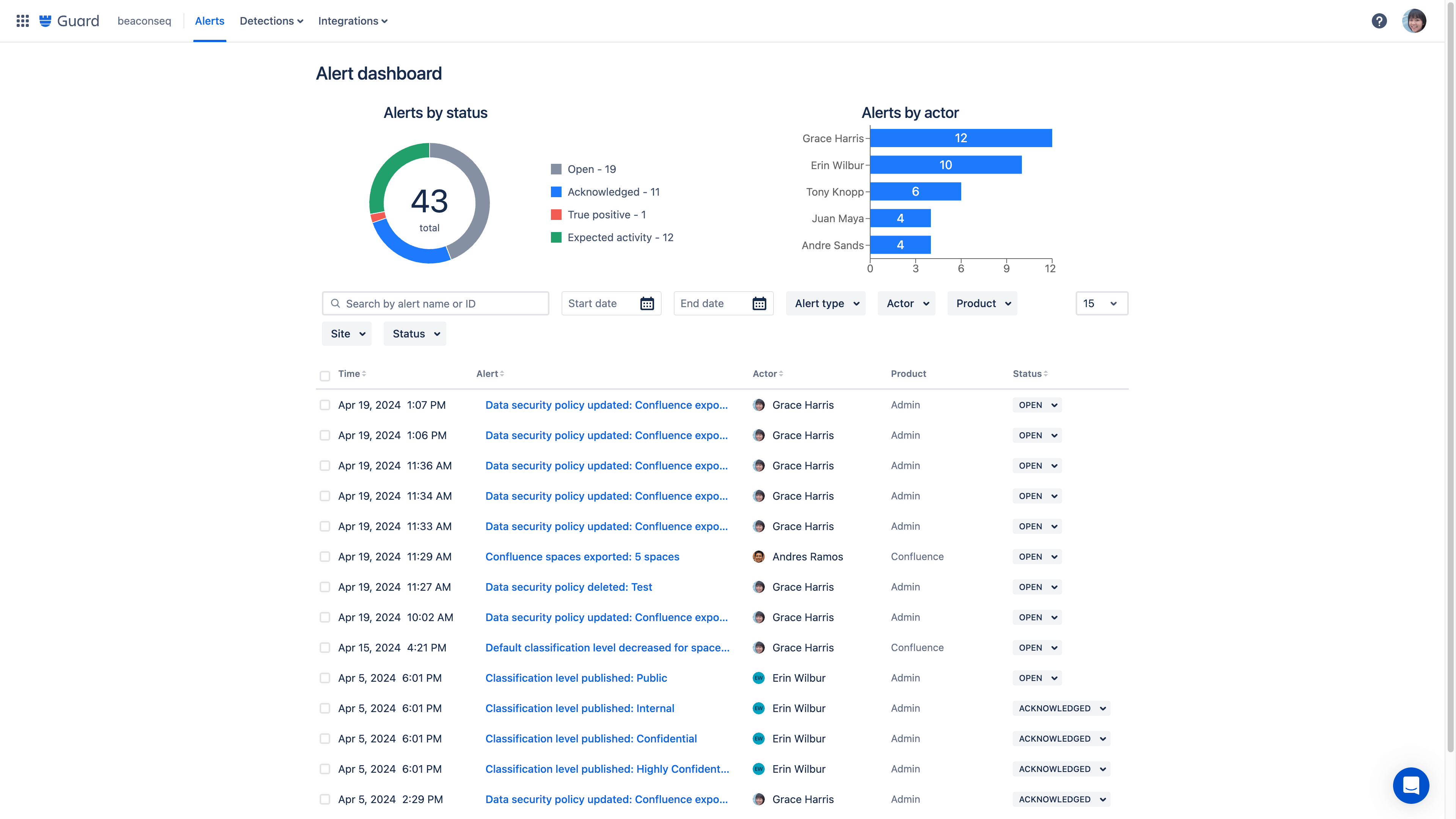
Alert investigations gives admins or security teams a consolidated view of potentially risky activity. Investigate the alert with details on what happened, which account was involved, other recent alerts tied to this account, and remediation options.
Actor profiles
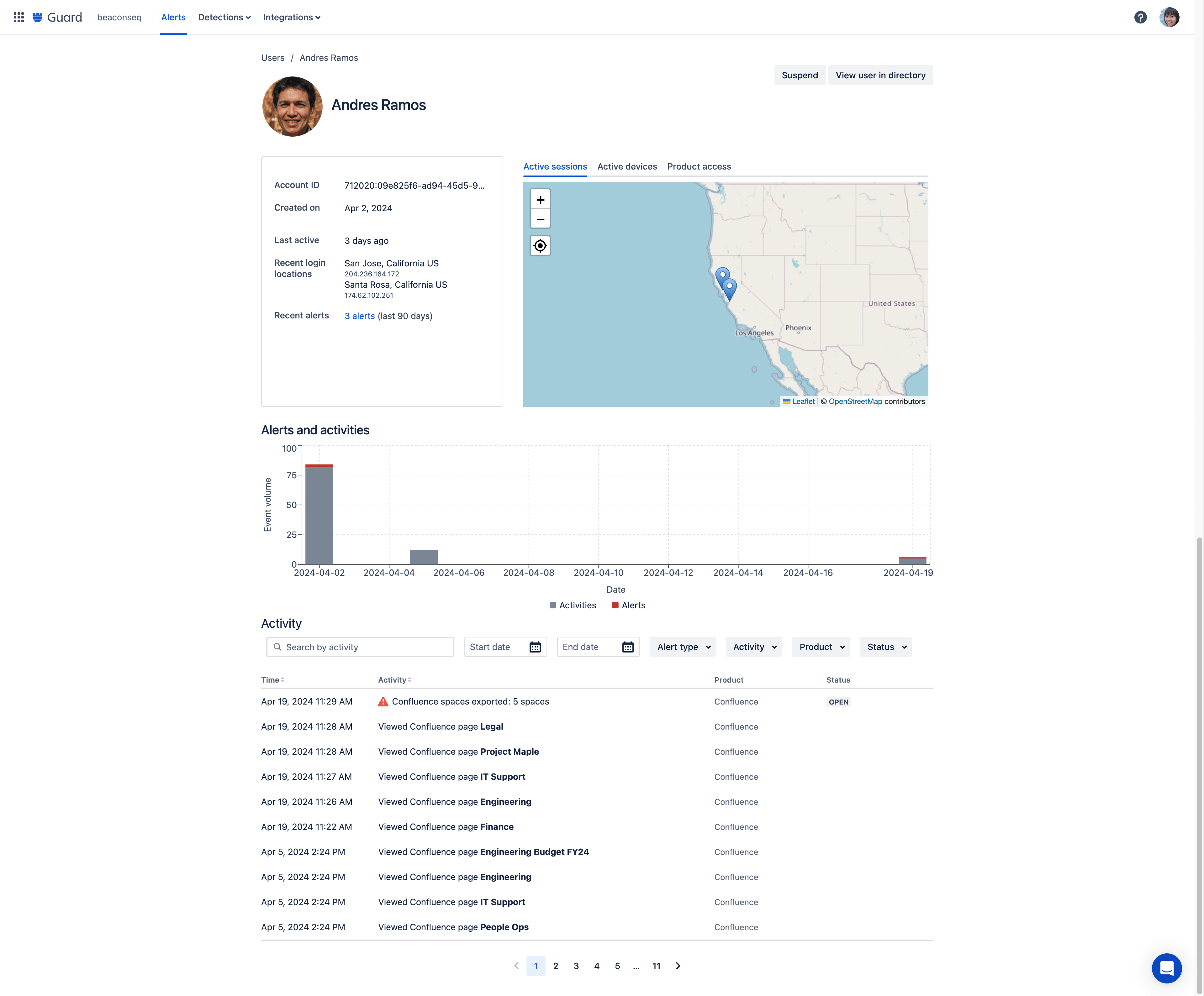
Access detailed user data by clicking into an actor profile directly from an alert to see a consolidated view of a user’s activity. On a single page, you can see a user’s role, location, recent activity, and a full list of their audit log alerts.
Remediation workflows
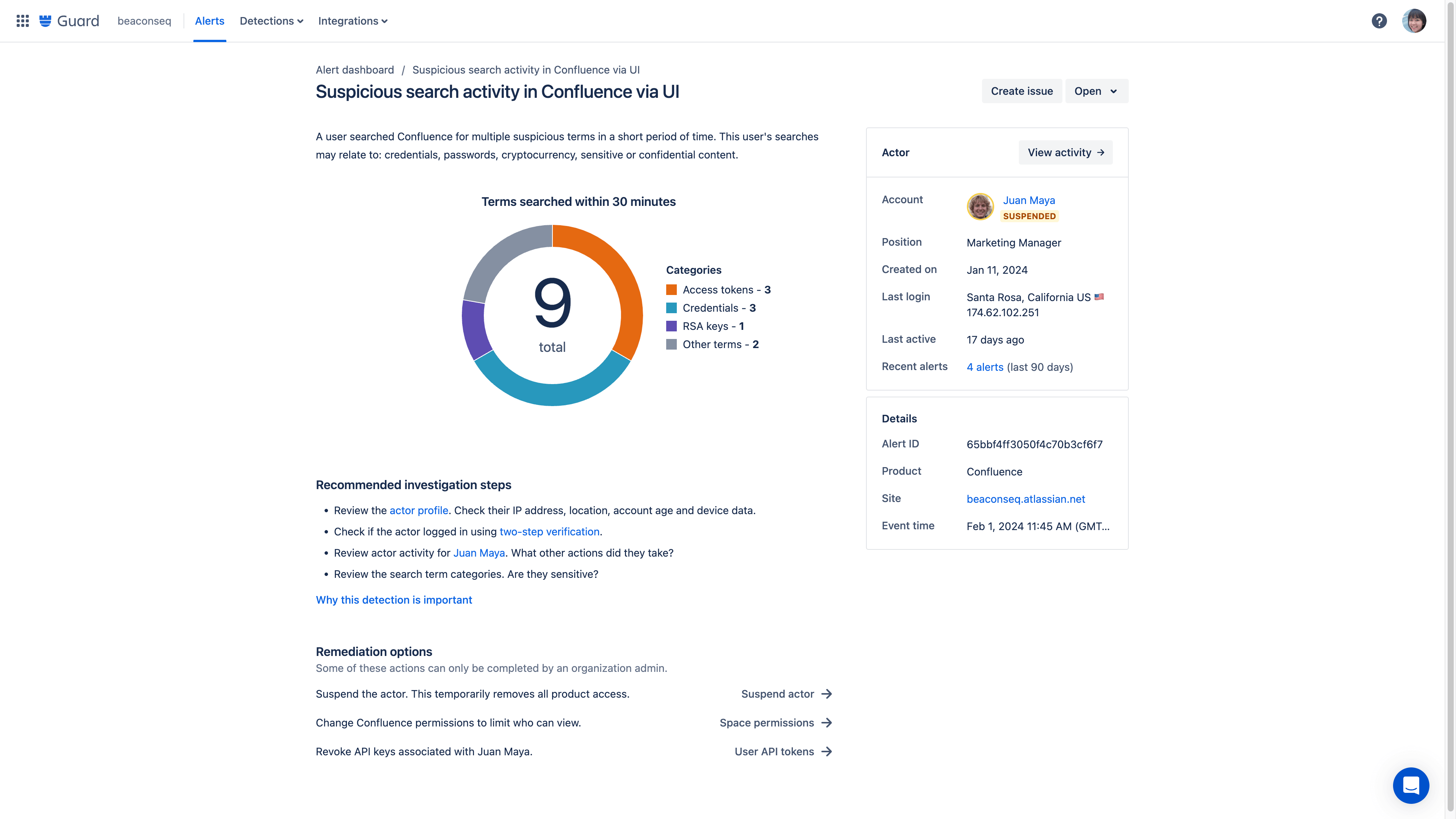
If suspicious behavior is detected, an organization admin can take action using the remediation recommendation to follow the suggested workflow and address a threat. Admins have the ability to immediately suspend a user's account directly from the alert dashboard.
Remediation recommendations
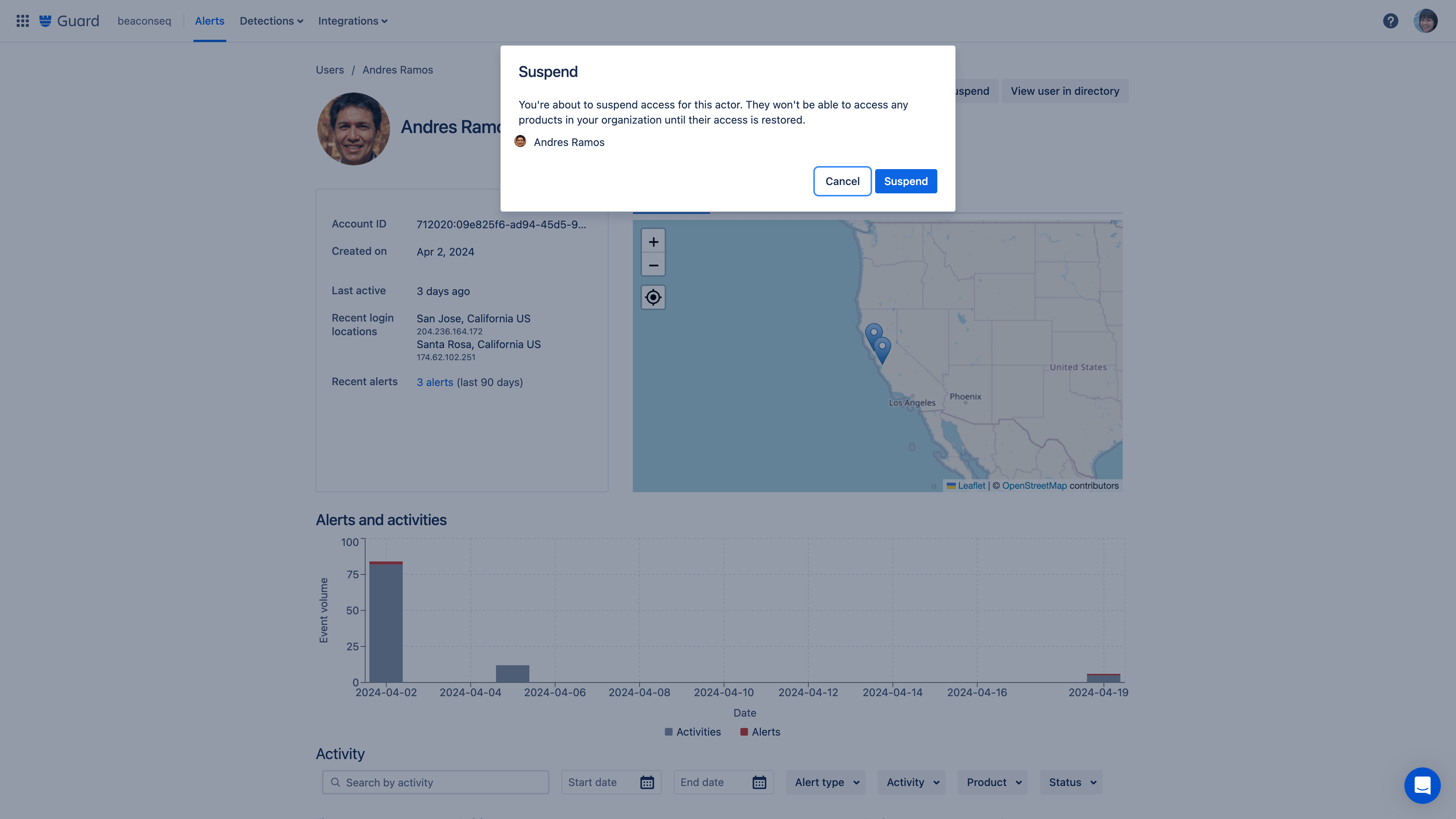
Respond to alerts faster with the ability to suspend a user’s account directly from the alert dashboard. Based on the actions logged in the dashboard, remediation options are recommended with actionable next steps.
Alert hand-off
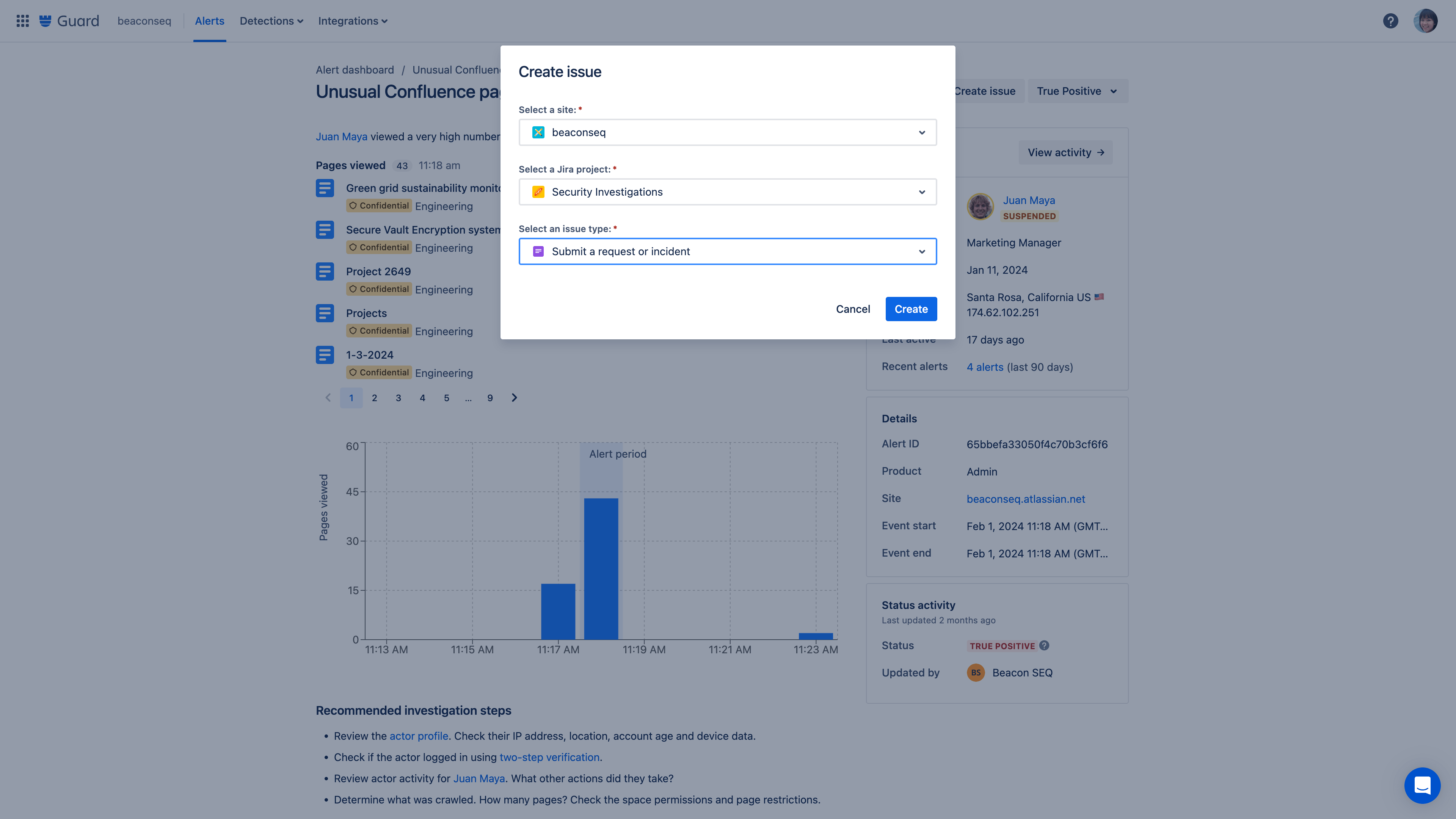
Connect an alert to Jira through the create issue button.
Questions about Atlassian Guard billing?
Visit our billing and licensing page for details.
Enforced two-step verification
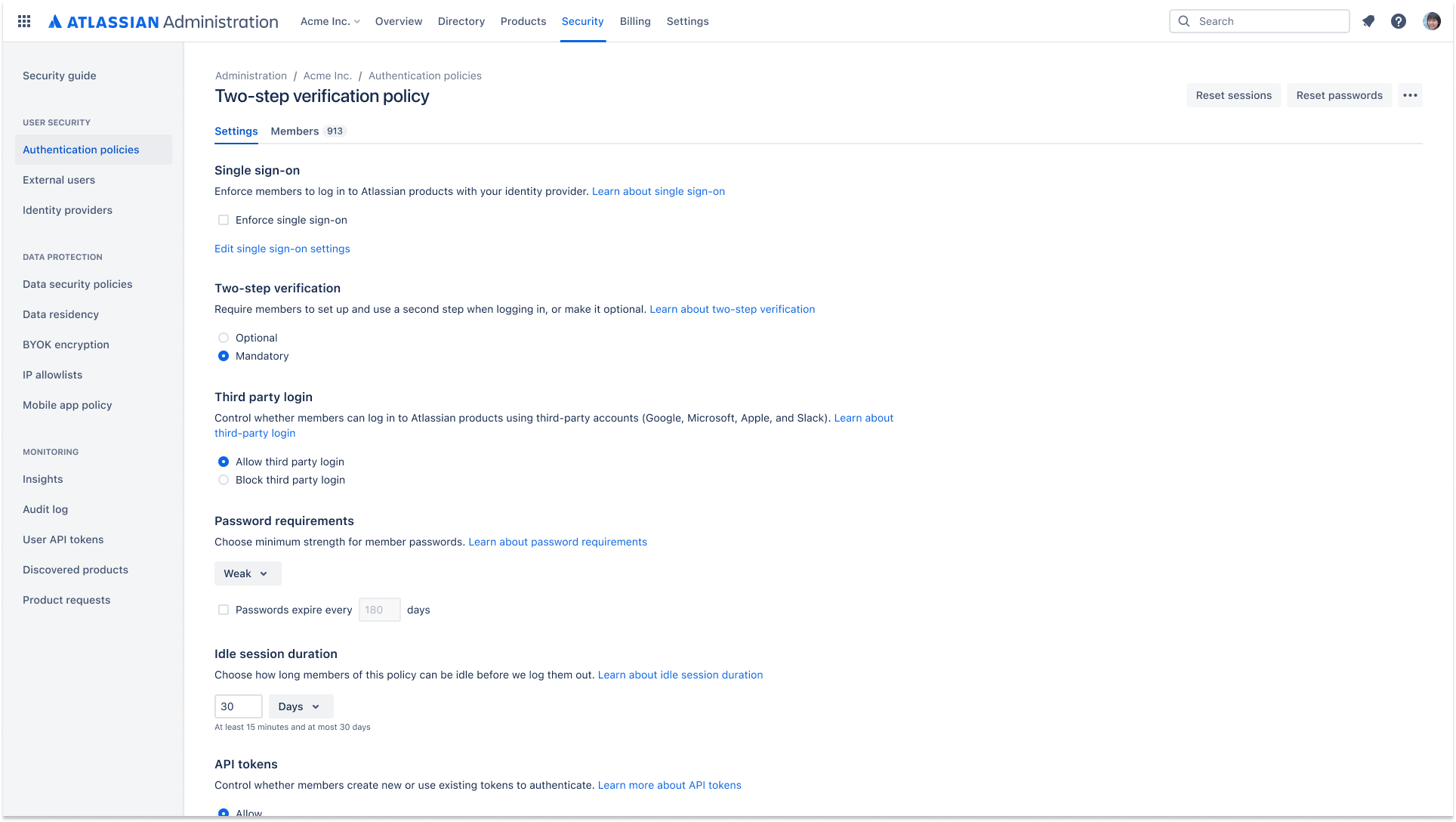
Enforced two-step verification can be applied as part of an authentication policy. This requires the users in an organization to turn on two-step verification in order to log in and access their Atlassian cloud products.