Gratis durante 30 días.
Comparar funciones
| Standard | Premium | |
| Protect against data loss proactively | ||
| Feature | Standard | Premium |
| Enforced single sign-on (SSO) ? | Standard ✓ | Premium ✓ |
| SCIM automated user provisioning ? | Standard ✓ | Premium ✓ |
| Authentication policies ? | Standard ✓ | Premium ✓ |
| External user security ? | Standard ✓ | Premium ✓ |
| Enforced two-step verification ? | Standard ✓ | Premium ✓ |
| Mobile app management (MAM) ? | Standard ✓ | Premium ✓ |
| API token controls ? | Standard ✓ | Premium ✓ |
| Data security policies ? | Standard ✓ | Premium ✓ |
| Data classification ? | Standard - | Premium ✓ |
| Enforce data security policies by classification ? | Standard - | Premium ✓ |
| Detect and investigate suspicious activity | ||
| Feature | Standard | Premium |
| Automatic product discovery ? | Standard ✓ | Premium ✓ |
| Organization insights ? | Standard ✓ | Premium ✓ |
| Organization audit log: Admin activity ? | Standard ✓ | Premium ✓ |
| Comprehensive organization audit log: User activity, API tokens, Webhooks ? | Standard - | Premium ✓ |
| Anomalous activity detections ? | Standard - | Premium ✓ |
| Content scanning ? | Standard - | Premium ✓ |
| SIEM integrations ? | Standard - | Premium ✓ |
| Alert messaging integrations ? | Standard - | Premium ✓ |
| Respond to threats before they become incidents | ||
| Feature | Standard | Premium |
| Alert investigations ? | Standard - | Premium ✓ |
| Actor profiles ? | Standard - | Premium ✓ |
| Remediation recommendations ? | Standard - | Premium ✓ |
| Remediation workflows ? | Standard - | Premium ✓ |
| Alert hand-off ? | Standard - | Premium ✓ |
See Atlassian Guard in action
Funciones de Atlassian Access
| El inicio de sesión único (SSO) es obligatorio para todos los usuarios gestionados puedan autenticarse en los productos de Atlassian Cloud a través del proveedor de identidades existente de la empresa. Esto implica que los usuarios pueden acceder a diferentes herramientas con el mismo conjunto de credenciales, haciendo uso de un método de autenticación más seguro que solo un nombre de usuario y una contraseña. |
| Automatiza la gestión del ciclo de vida de los usuarios con el aprovisionamiento y el desaprovisionamiento de SCIM. El acceso a los productos de Atlassian Cloud se definirá conforme a las reglas definidas en tu directorio externo. El aprovisionamiento de usuarios reduce el trabajo manual que supone dar acceso a los empleados a la aplicación cuando se unen a la empresa o se pasan a un equipo nuevo. |
| Los administradores pueden definir políticas de autenticación para gestionar la duración de la sesión, el inicio de sesión único (SSO), las políticas de contraseñas y la verificación en dos pasos. Se pueden crear varias políticas y aplicarlas a subconjuntos de cuentas gestionadas distintos. |
| La verificación obligatoria en dos pasos se puede aplicar dentro de una política de autenticación. Para ello, los usuarios de una organización deben activar la verificación en dos pasos para iniciar sesión y acceder a sus productos de Atlassian Cloud. |
| Crea y gestiona políticas de seguridad que se puedan aplicar tanto a los usuarios gestionados como a los no gestionados con la gestión de aplicaciones móviles (MAM, por sus siglas en inglés). Las políticas se pueden definir a escala de la organización o designar para determinados usuarios a fin de proporcionar controles de seguridad adicionales como, por ejemplo, deshabilitar las capturas de pantalla, restringir la exportación de datos y exigir el cifrado de los dispositivos. |
| Obtén visibilidad de la shadow IT descubriendo cuándo crean instancias en los productos de Atlassian Cloud los usuarios gestionados de tu organización. La detección automática de productos identifica al administrador del producto y la cantidad de usuarios que utilizan estos productos. |
| Un registro integral de la actividad de administración que tiene lugar en tu organización de Atlassian Cloud. Un registro de auditoría de la organización muestra a los administradores el quién, el qué y el cuándo de la actividad administrativa para ayudar a las organizaciones a rastrear e identificar cualquier comportamiento sospechoso. |
| Integra Atlassian Access con tu CASB para capturar un registro completo de la actividad administrativa y de inicio de sesión en Atlassian. Defiéndete de amenazas habituales como, por ejemplo, las credenciales de usuario comprometidas, la deficiente protección de las contraseñas, o las amenazas internas por cuentas que tienen un exceso de privilegios. Más información sobre cómo conectar tus CASB de McAfee MVISION o Microsoft Defender. |
Enforced single sign-on (SSO)
Nota: Para que la tabla sea sencilla, solo se muestran hasta 5000 usuarios. Access no tiene límite de usuarios. Utiliza la calculadora de precios para saber el precio anual de más de 5000 usuarios.
SCIM automated user provisioning
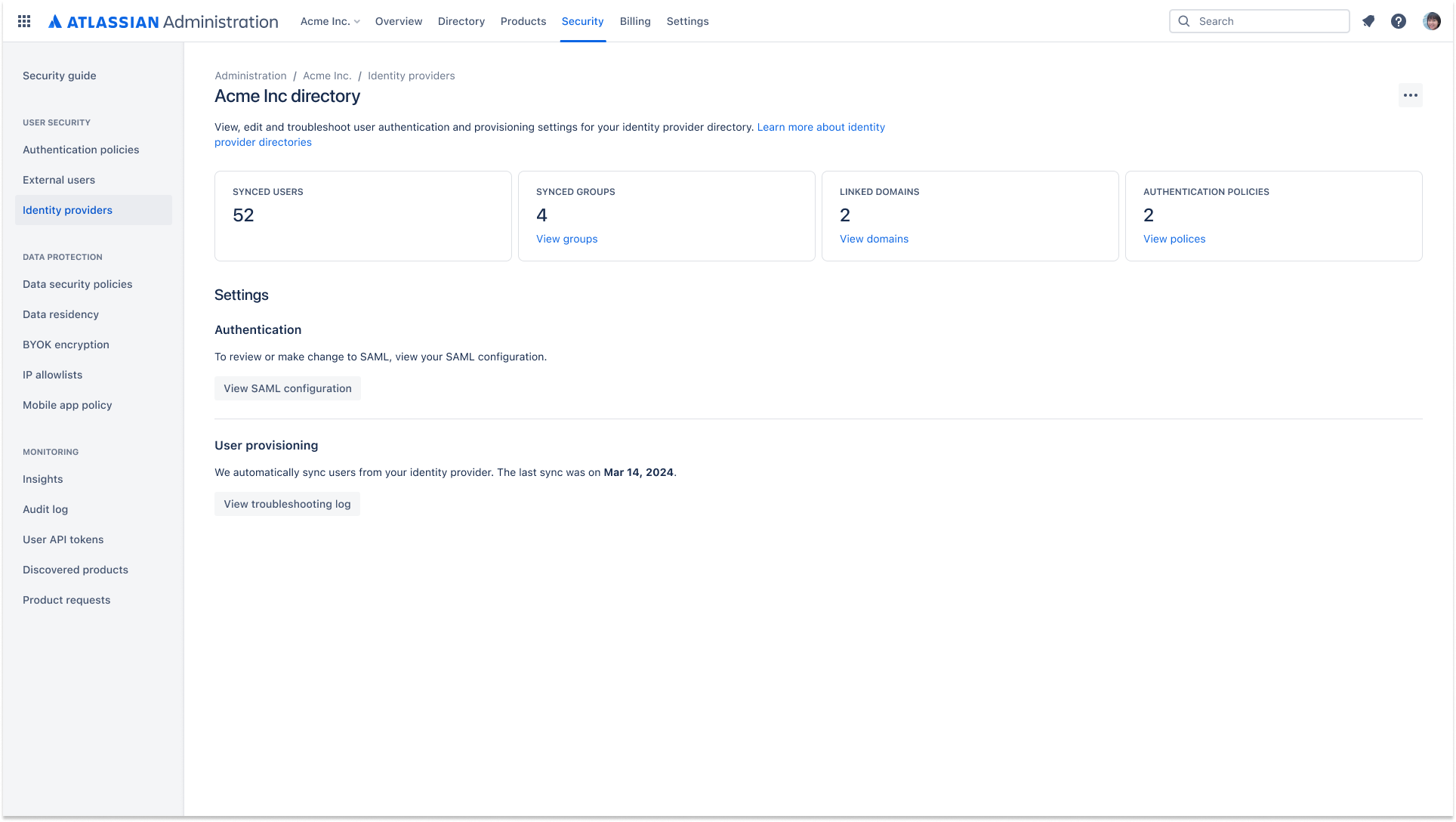
Automate user lifecycle management with SCIM provisioning and de-provisioning. Access to Atlassian cloud products will be defined by rules set in your external directory.
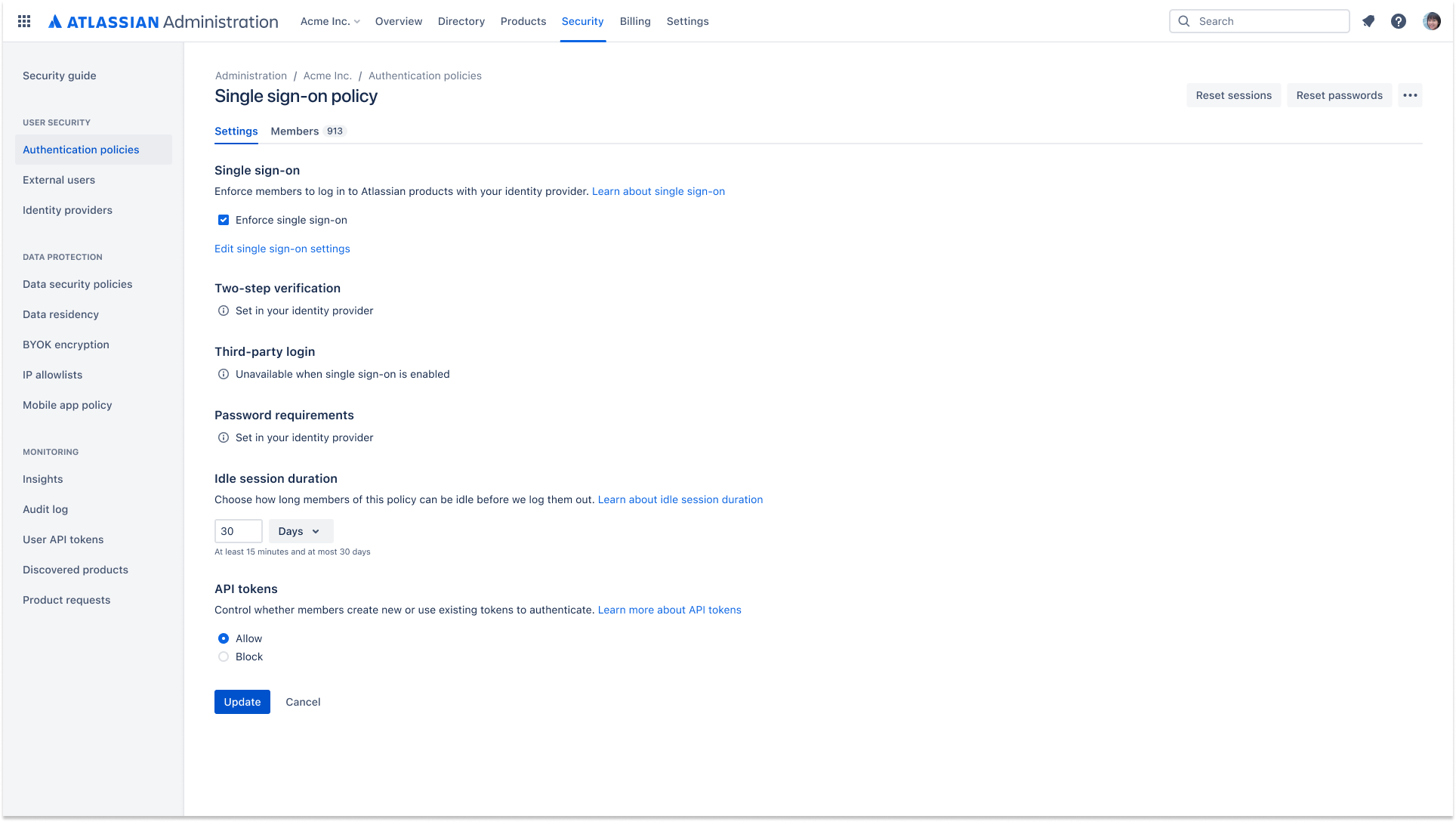
Authentication policies
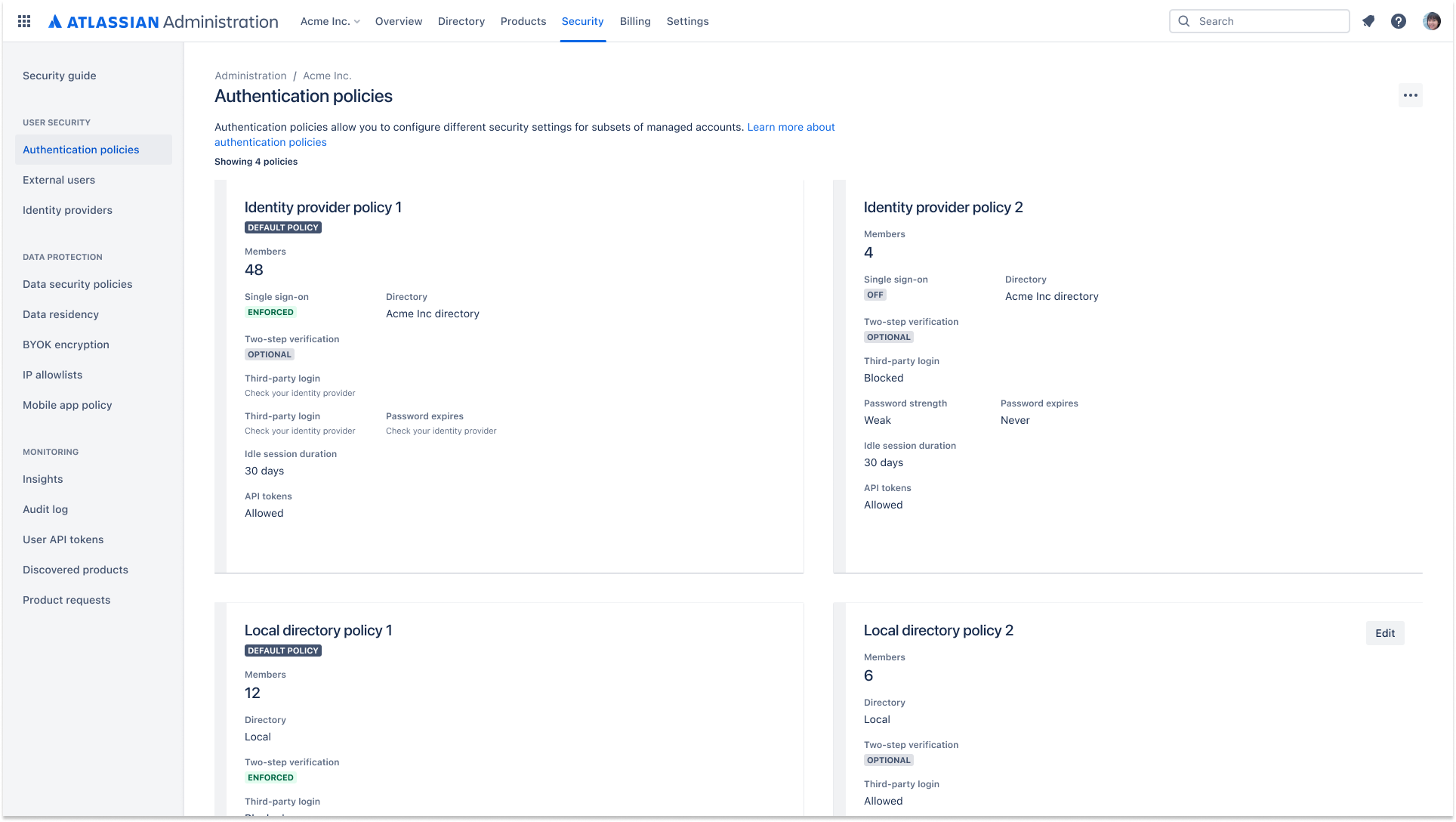
Admins can set authentication policies to manage session duration, single sign-on (SSO), password policies, and two-step verification. Multiple policies can be created and applied to different subsets of managed accounts.
External user security
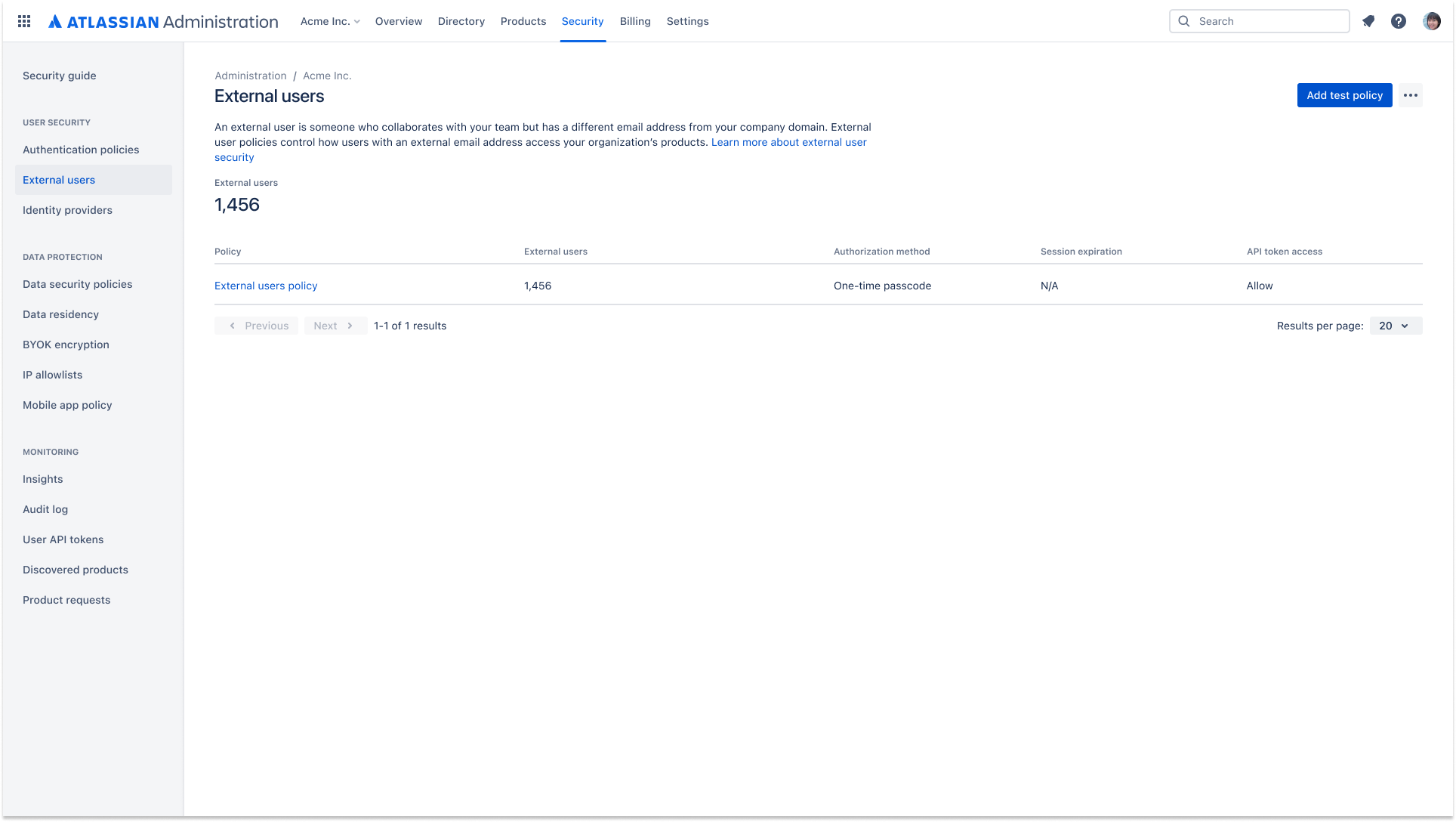
An external user policy allows you to apply security settings, including two-step verification, to external users. The settings apply to all the external users in your Atlassian organization.
Mobile app management (MAM)
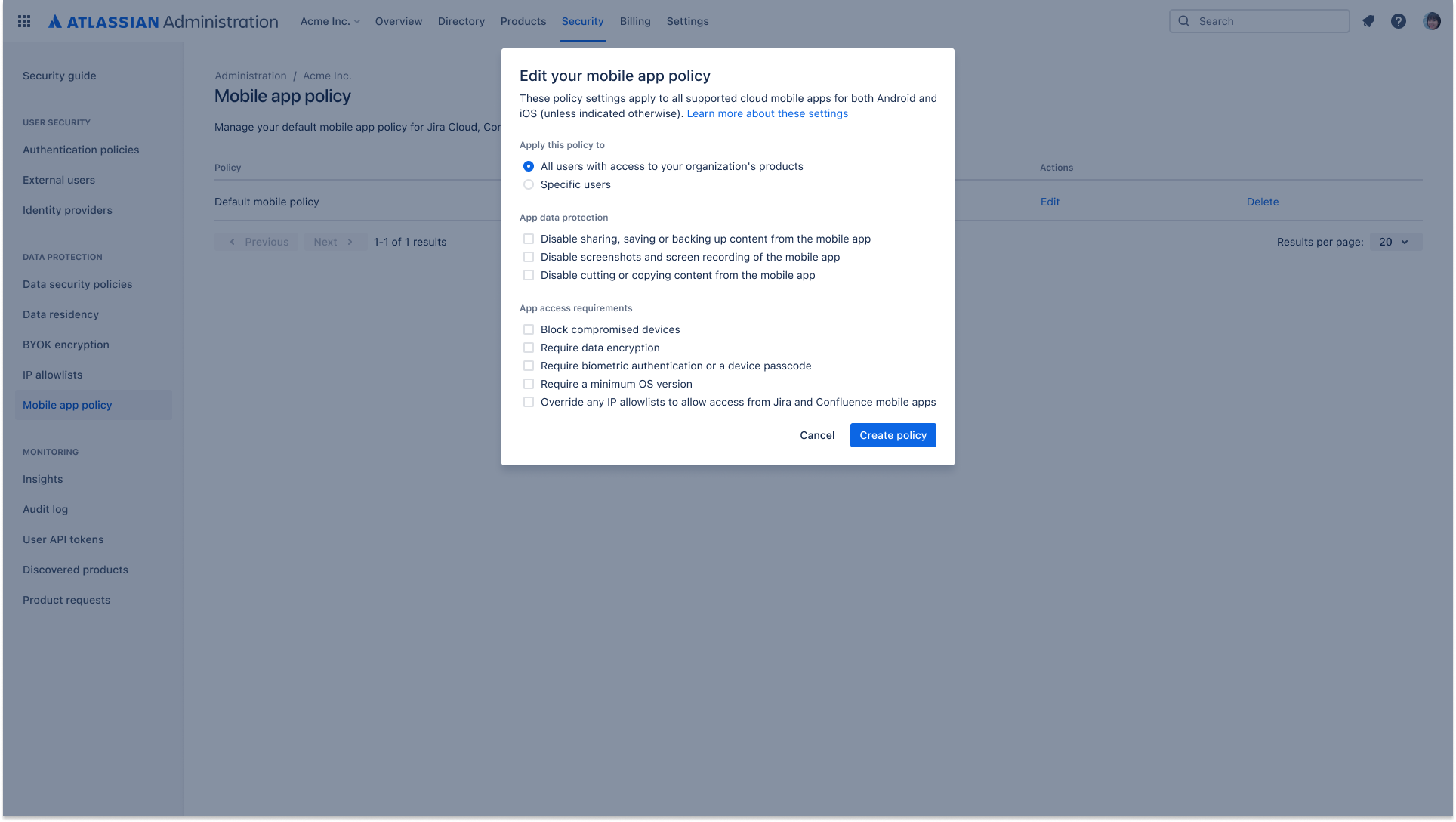
Create and manage security policies that can be applied to both managed and unmanaged users with mobile app management (MAM). Policies can be set at the organization level, or designated for select users to provide additional security controls such as screenshot disabling, data export restrictions and device encryption requirements
API token controls
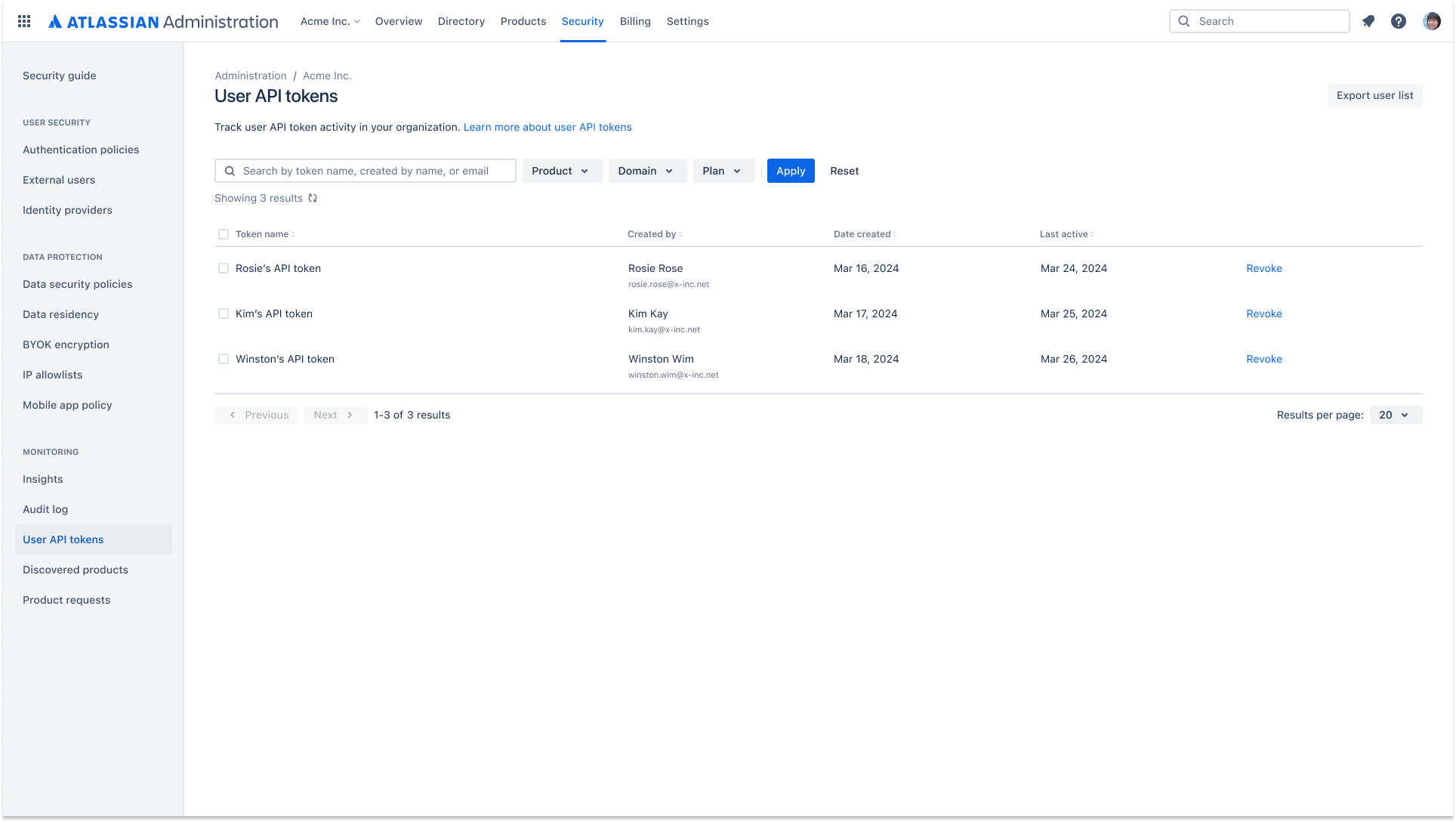
Admins have greater visibility and control over API token management and its lifecycle. This includes controlling which users can create an API token to access data and viewing which users are creating and revoking API tokens.
Data security policies
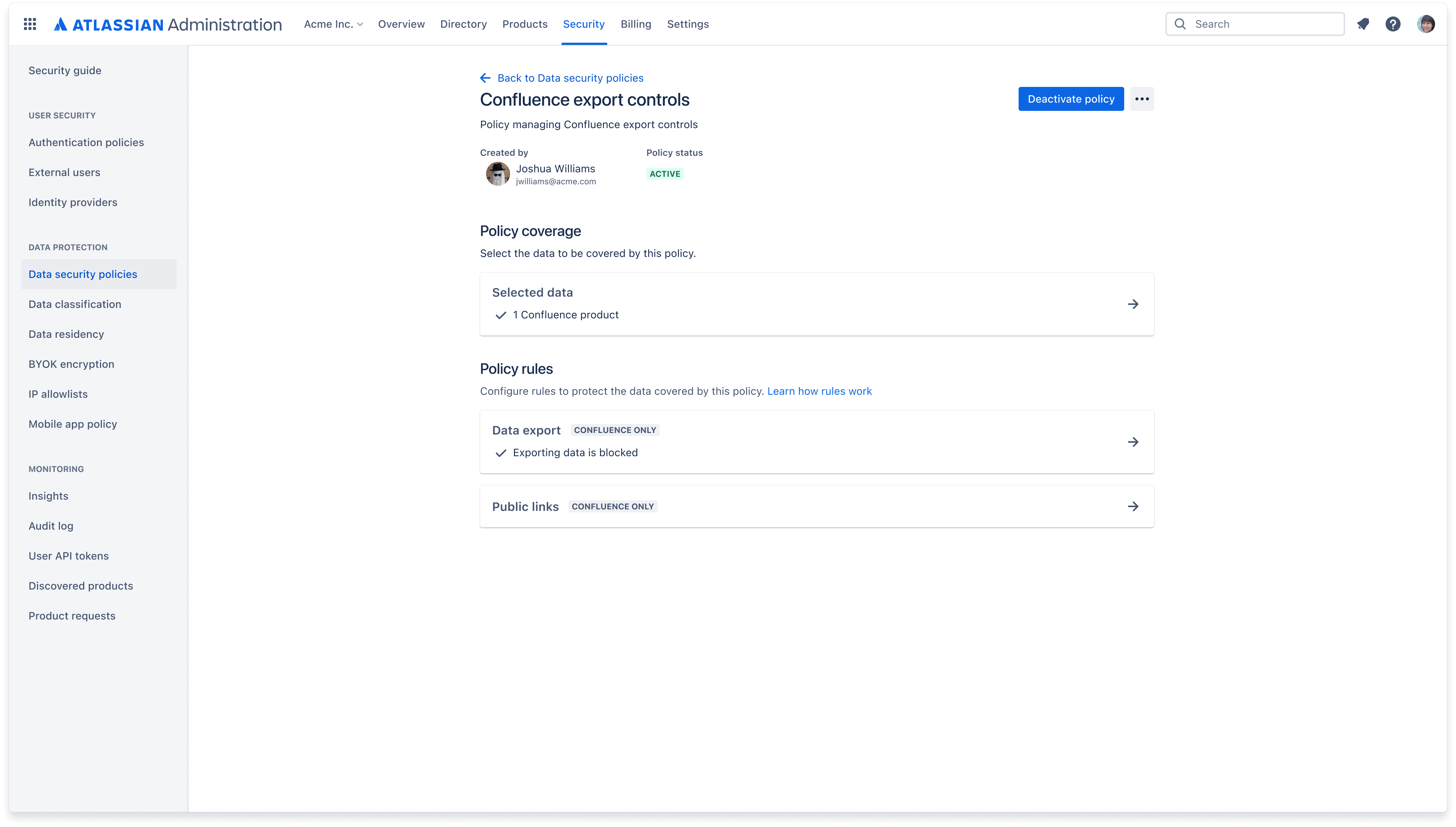
A data security policy helps you keep your organization’s data secure. Create policies to govern how users, apps, and people outside of your organization can interact with content such as Confluence pages and Jira issues.
Data classification
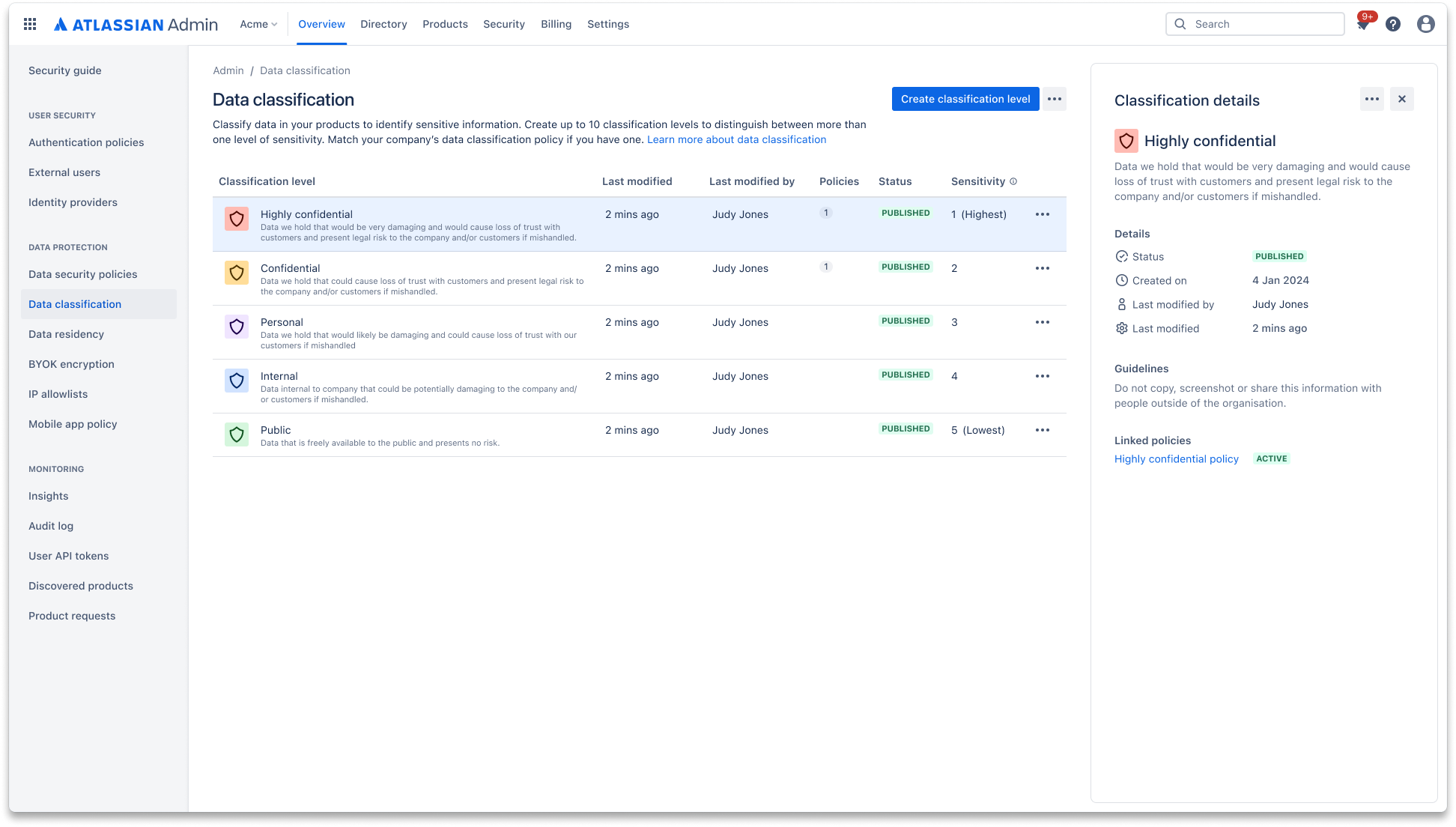
Data classification allows admins to define their data governance approach and label critical data accordingly within Atlassian products. Admins can set data security policies and rules to control user interaction based on data classification level.
Enforce data security policies by classification
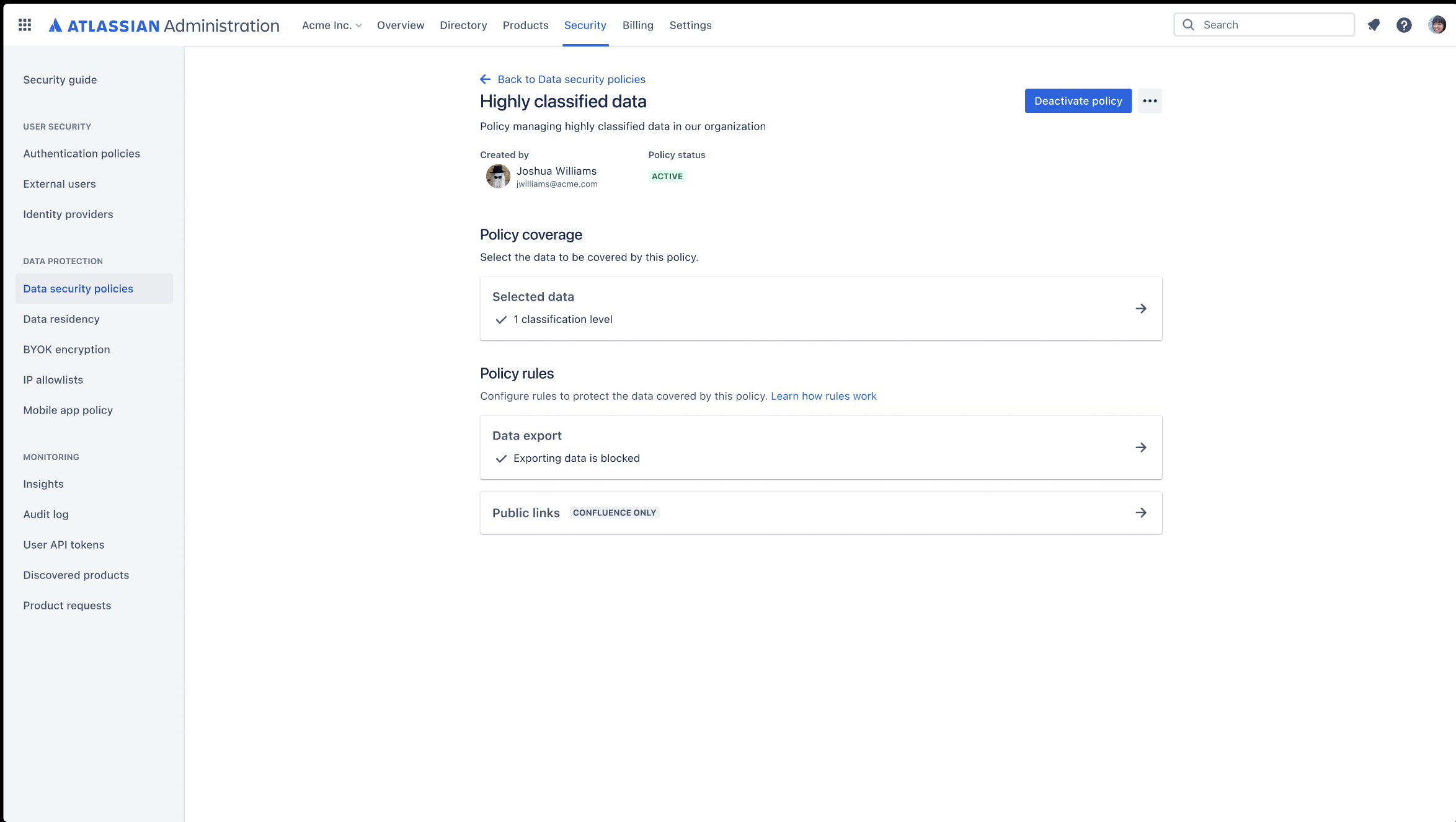
Use data classification levels as a coverage in your data security policy. Create policies to govern how users, apps, and people outside of your organization can interact with content such as Confluence pages and Jira issues.
Use data classification to set additional rules within your data security policy, including: "Block Export" rule in Confluence and Jira, “Anonymous Access” rule in Jira, and “Block Public Links” rule in Confluence using classification.
Automatic product discovery
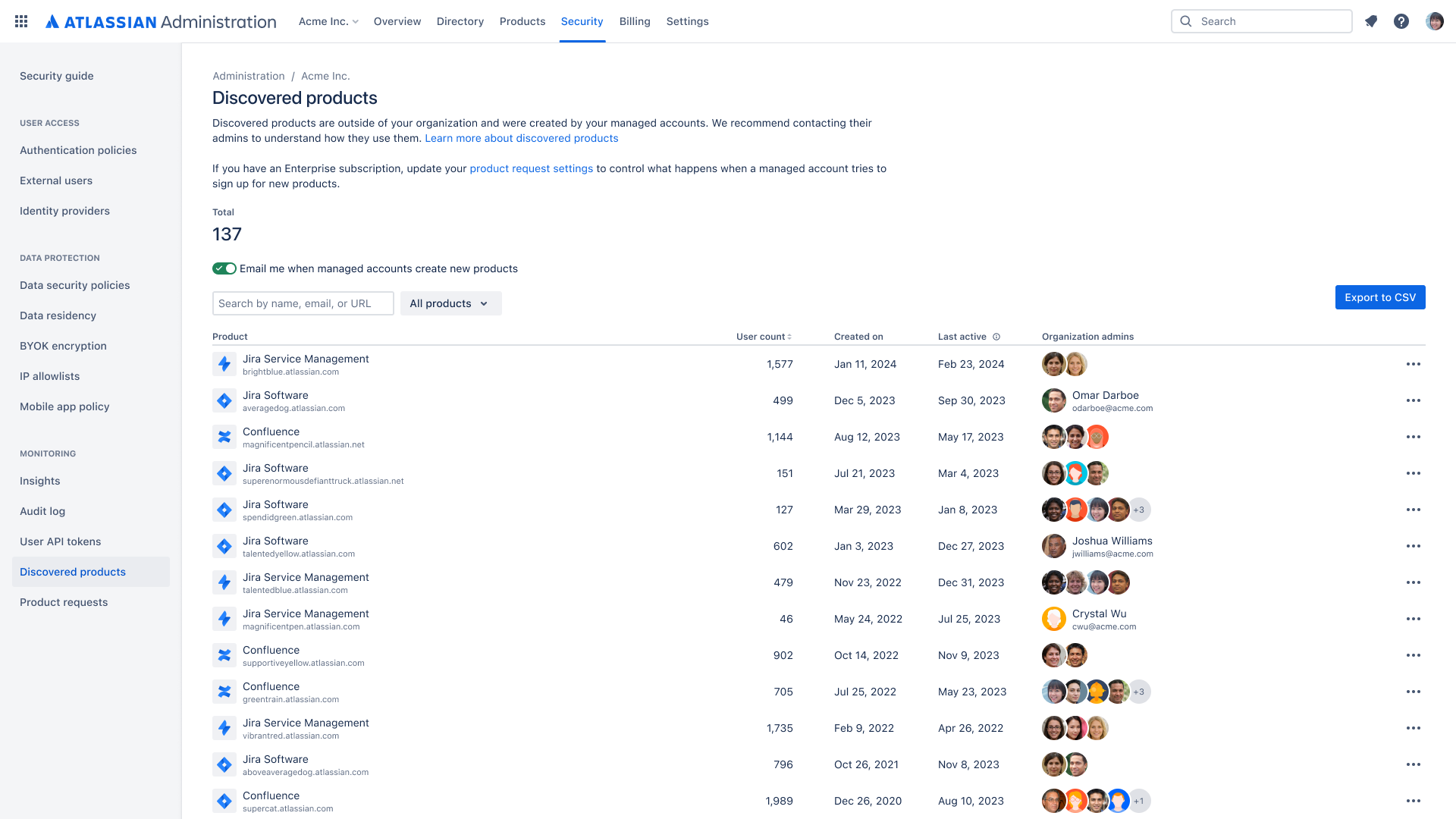
Gain visibility into shadow IT by discovering when managed users in your organization create instances across Atlassian cloud products. Automatic product discovery identifies the product administrator and how many users are using these products.
Organization insights
Admins can achieve better visibility into the usage of their Atlassian products and make more data-driven decisions when it comes to increasing adoption or optimizing their products' ROI.
Organization audit log: Admin activity
79b0.png)
A centralized log of admin activity across your Atlassian cloud organization. Gain a full view of the who, what, and when of admin activity to help track and identify any suspicious behavior. Using APIs, integrate with your third party tools, such as a CASB.
Comprehensive organization audit log: User activity, API tokens, Webhooks
79b0.png)
A comprehensive log of org admin, product admin, and user activity that takes place in the Atlassian cloud organization. This provides organization admins with visibility into activities like which managed users have created an API token or what organizational resources are being accessed by managed and external users via API tokens. Audit log webhooks are customized HTTP callbacks that trigger in response to audit log events.
Anomalous activity detections
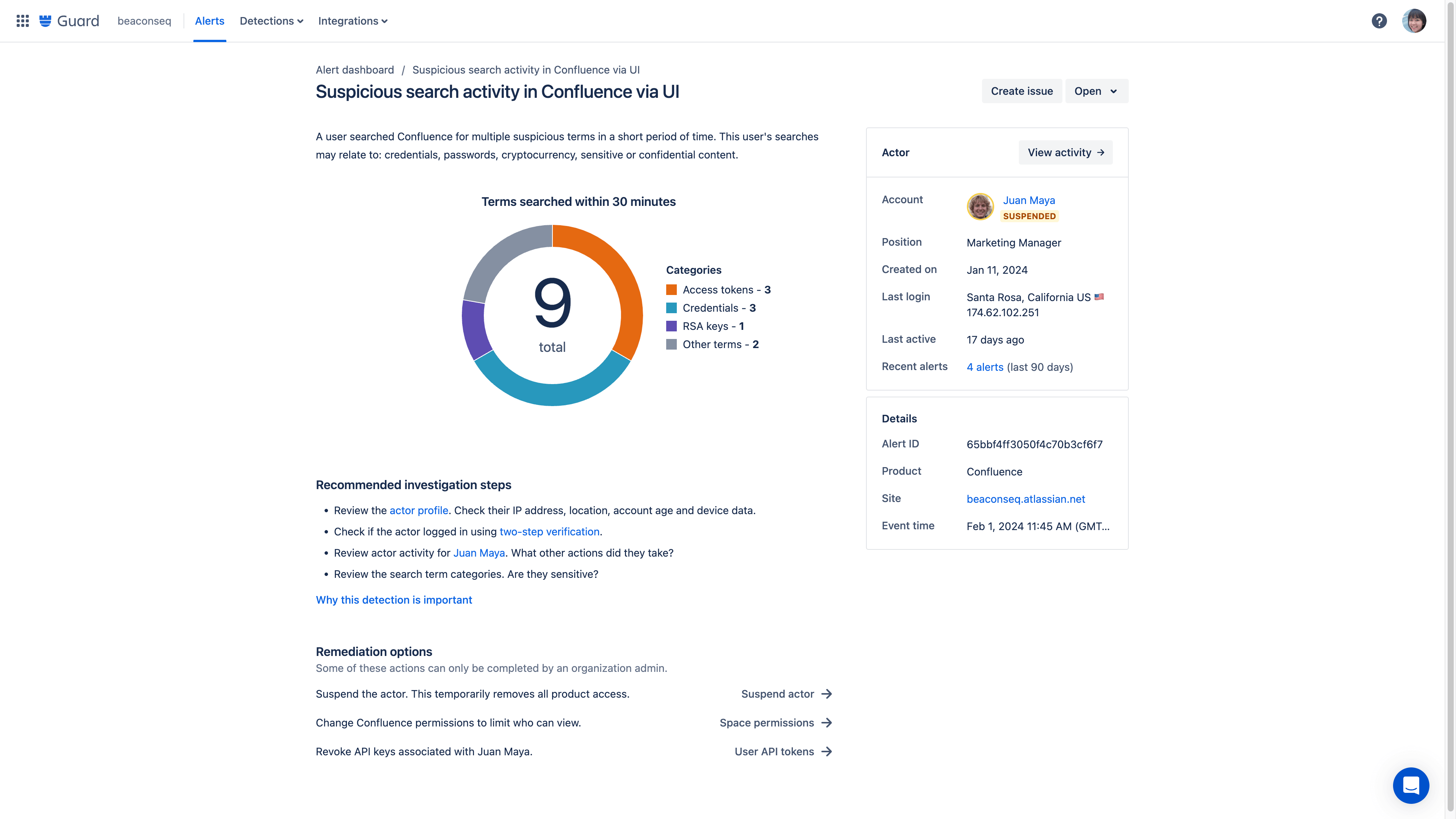
Anomalous activity detections provide intelligent oversight across your Atlassian cloud products by analyzing user activity and notifying you of potential risks. These queries search activity logs and alert you to any potentially concerning activity that requires review.
Content scanning
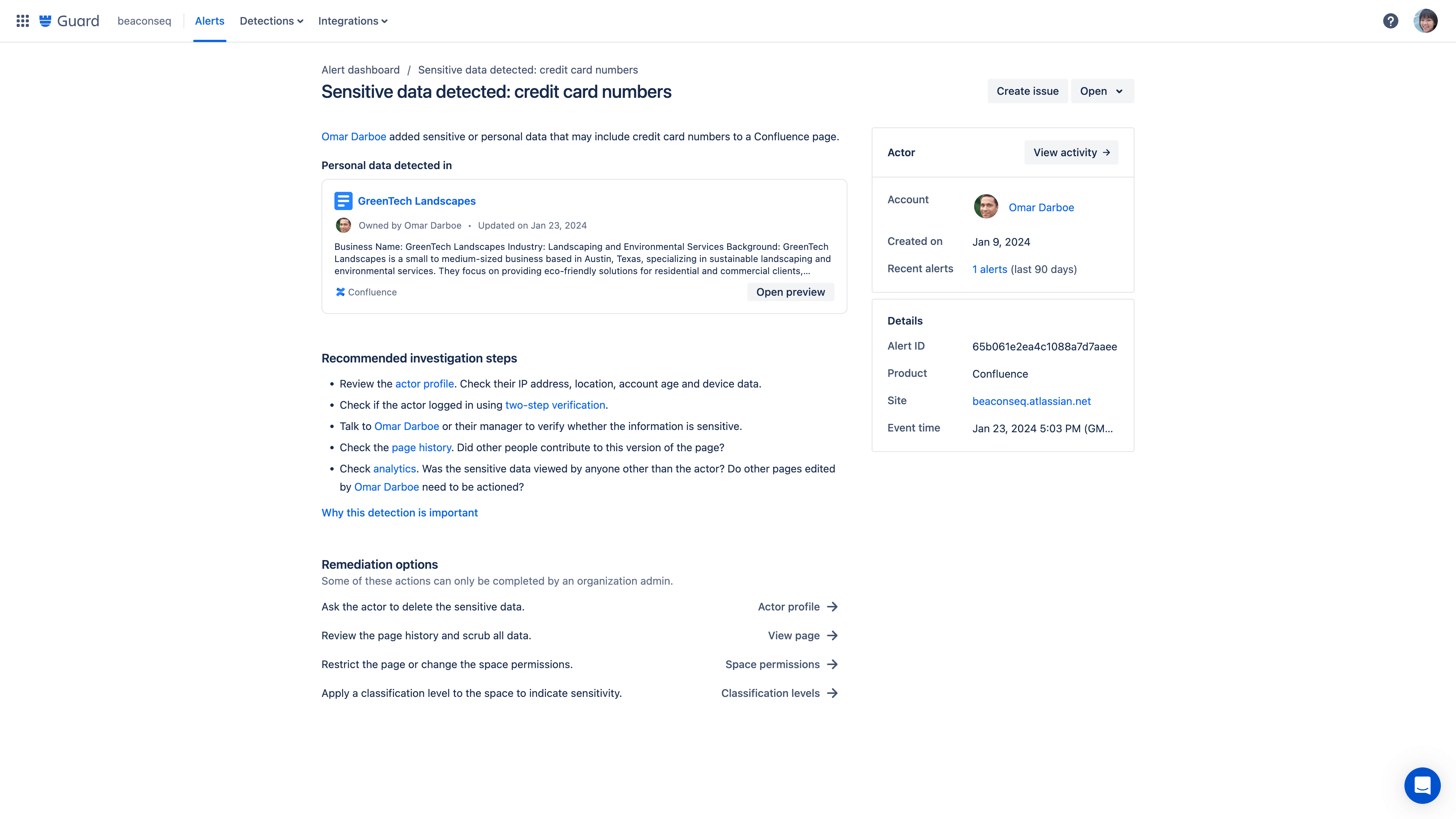
Content scanning detection rules monitor for critical data being added to Confluence pages. These detections generate alerts for any potentially concerning content that requires review.
SIEM integrations
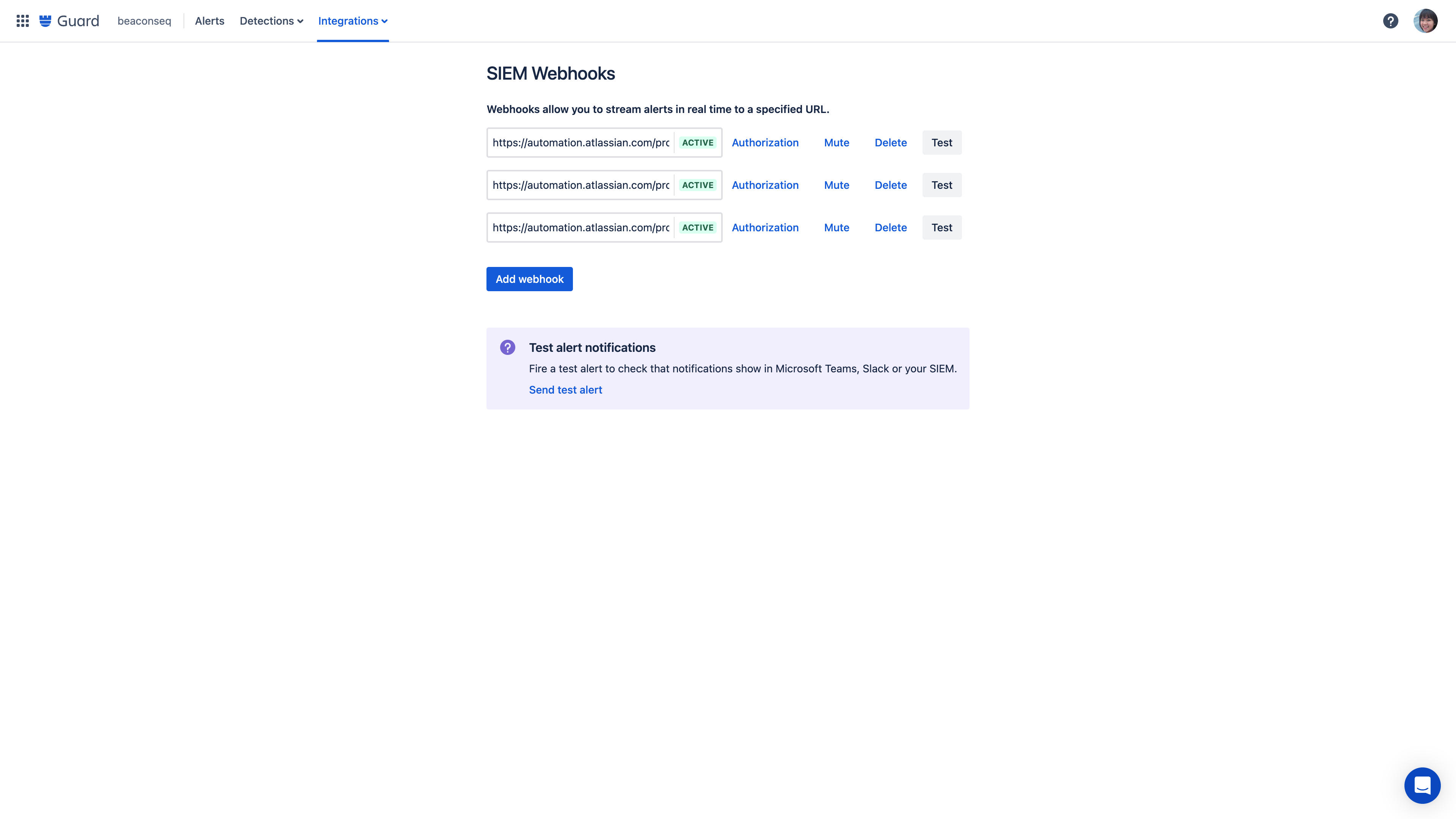
Using webhooks, send alerts about anomalous activity to any destination, including your organization-wide SIEM or an automation tool like Jira Automation, Zapier, or Workato.
Alert messaging integrations
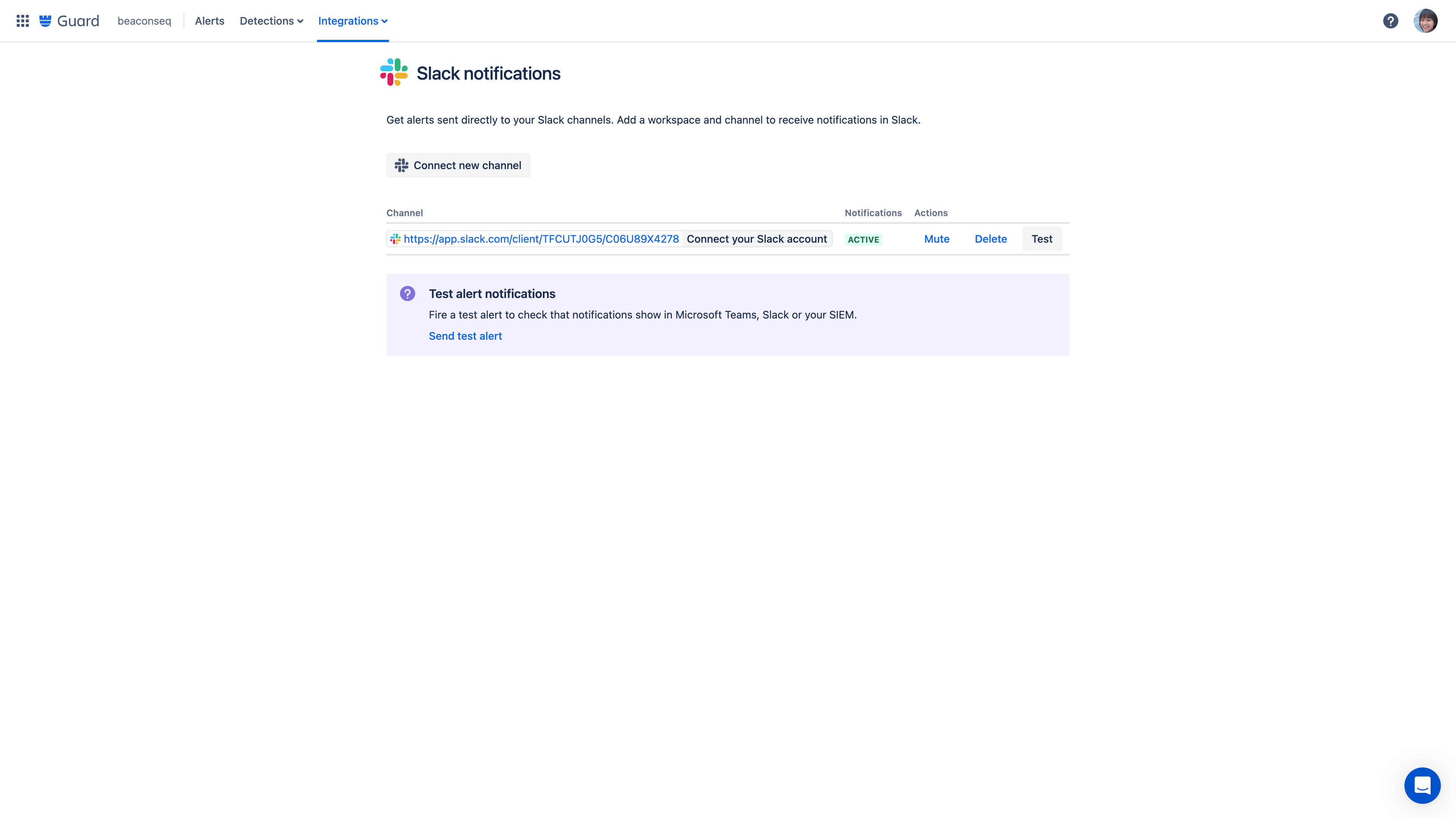
Integrate alert messages to your organization-wide tools like Slack, Microsoft Teams, and more.
Alert investigations
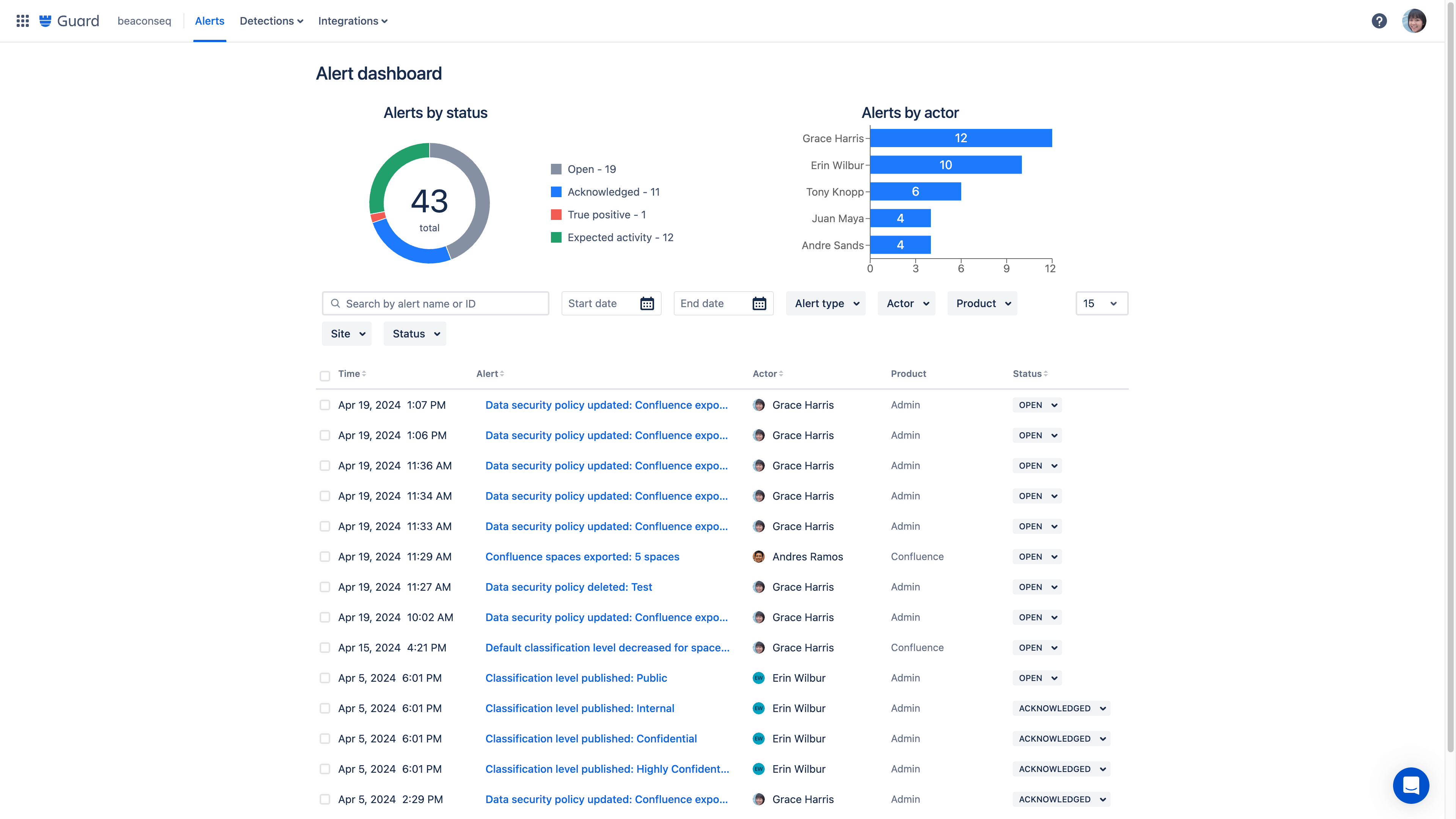
Alert investigations gives admins or security teams a consolidated view of potentially risky activity. Investigate the alert with details on what happened, which account was involved, other recent alerts tied to this account, and remediation options.
Actor profiles
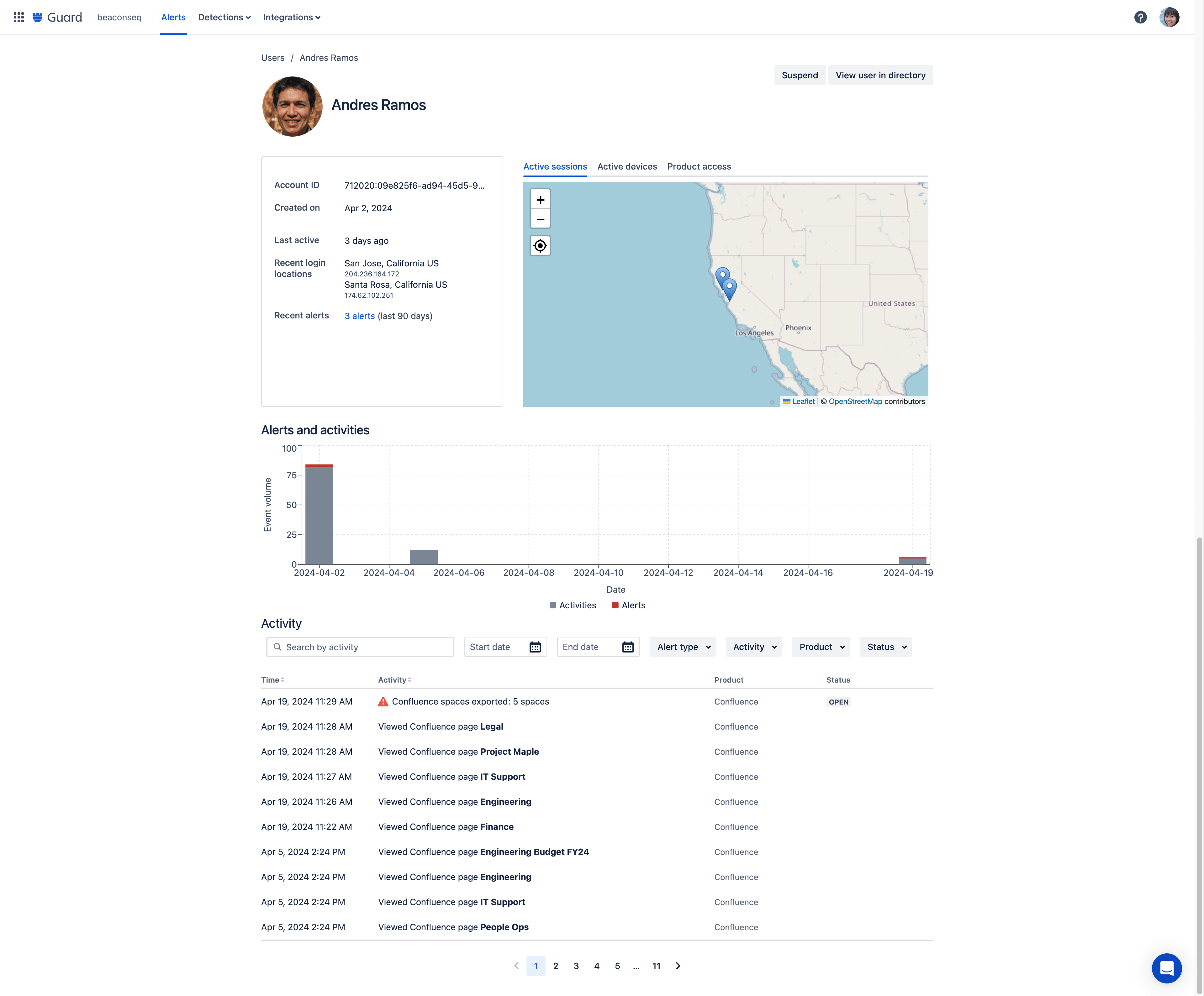
Access detailed user data by clicking into an actor profile directly from an alert to see a consolidated view of a user’s activity. On a single page, you can see a user’s role, location, recent activity, and a full list of their audit log alerts.
Remediation workflows
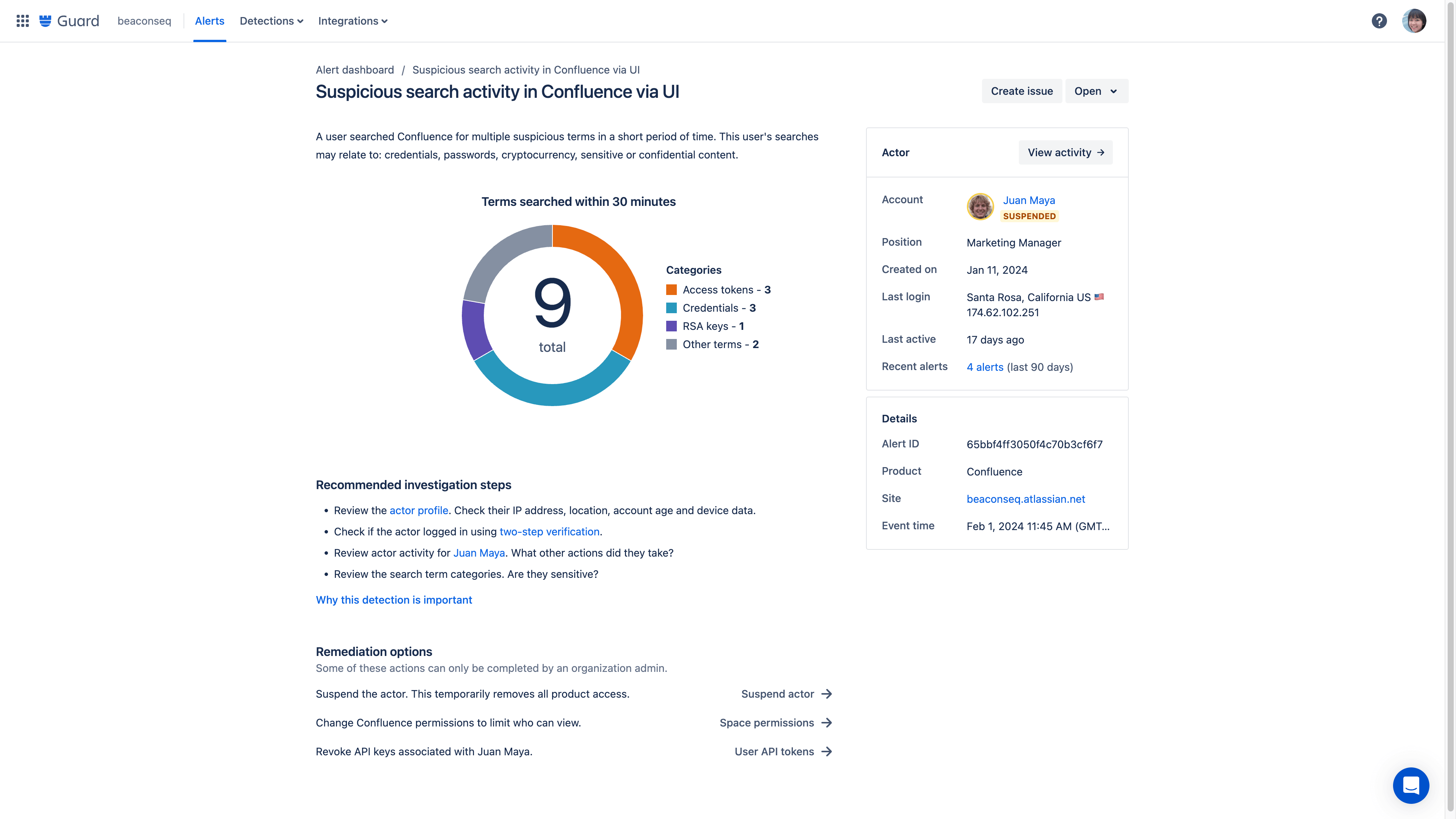
If suspicious behavior is detected, an organization admin can take action using the remediation recommendation to follow the suggested workflow and address a threat. Admins have the ability to immediately suspend a user's account directly from the alert dashboard.
Remediation recommendations
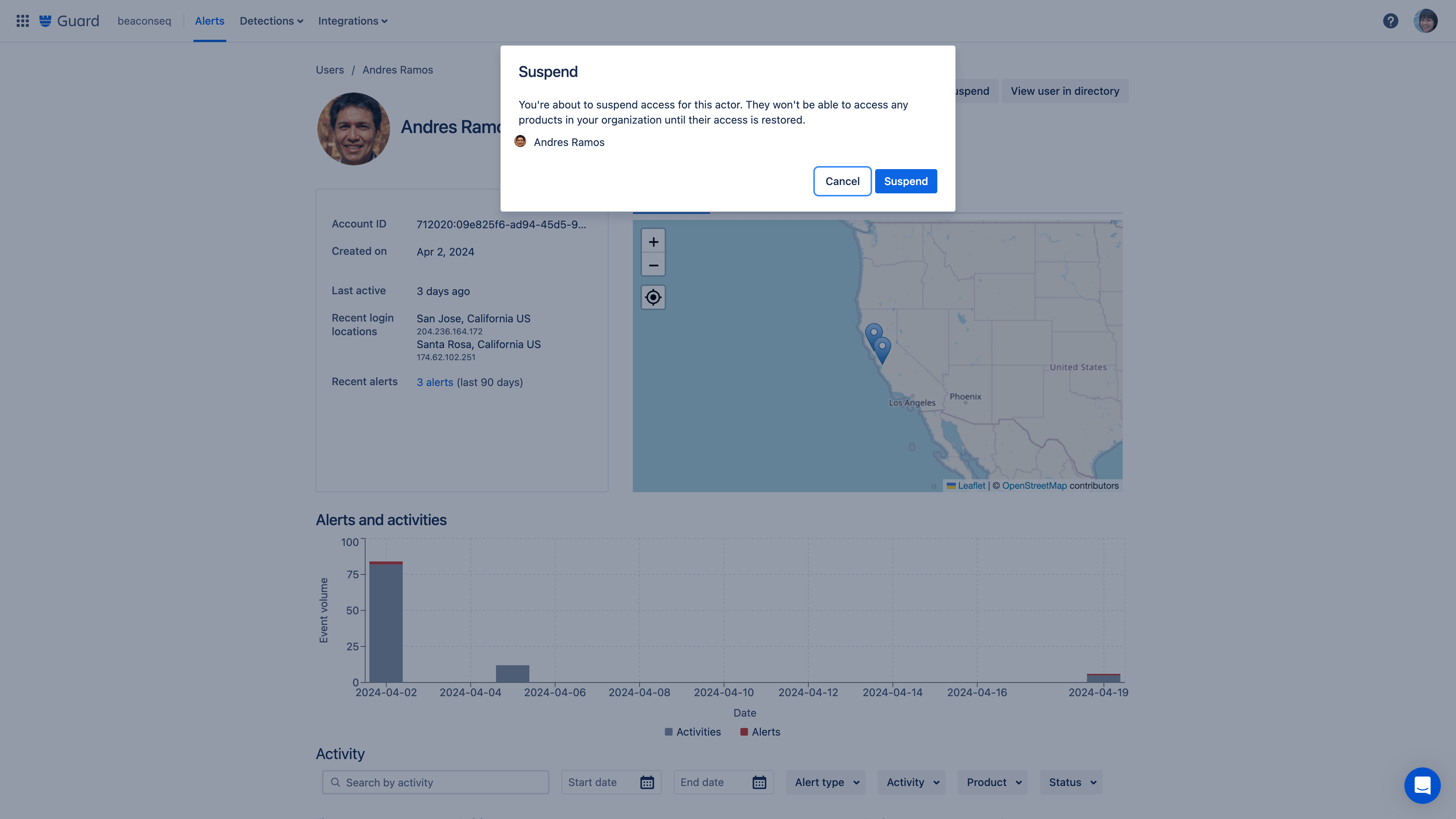
Respond to alerts faster with the ability to suspend a user’s account directly from the alert dashboard. Based on the actions logged in the dashboard, remediation options are recommended with actionable next steps.
Alert hand-off
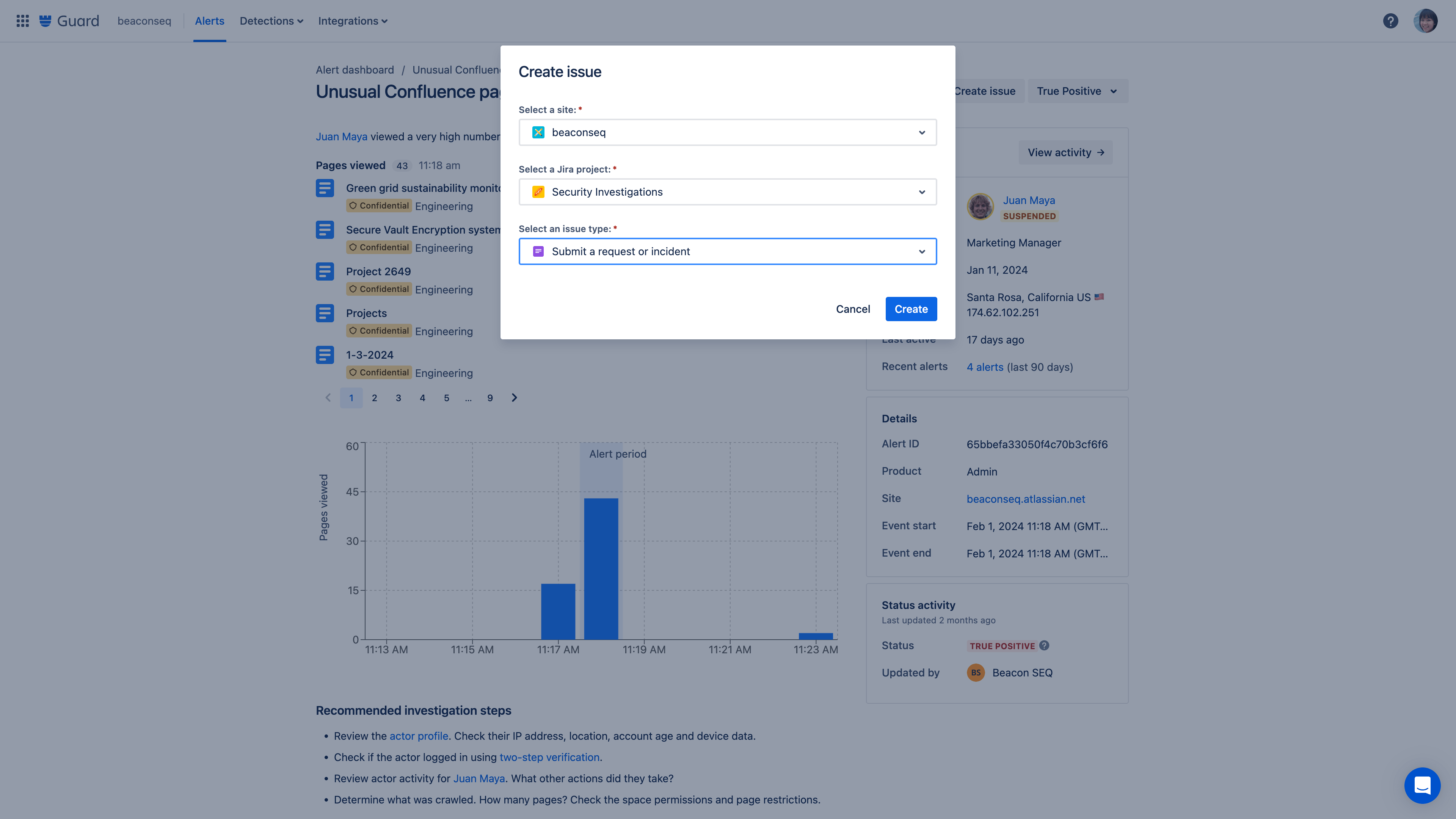
Connect an alert to Jira through the create issue button.
Questions about Atlassian Guard billing?
Visit our billing and licensing page for details.
Enforced two-step verification
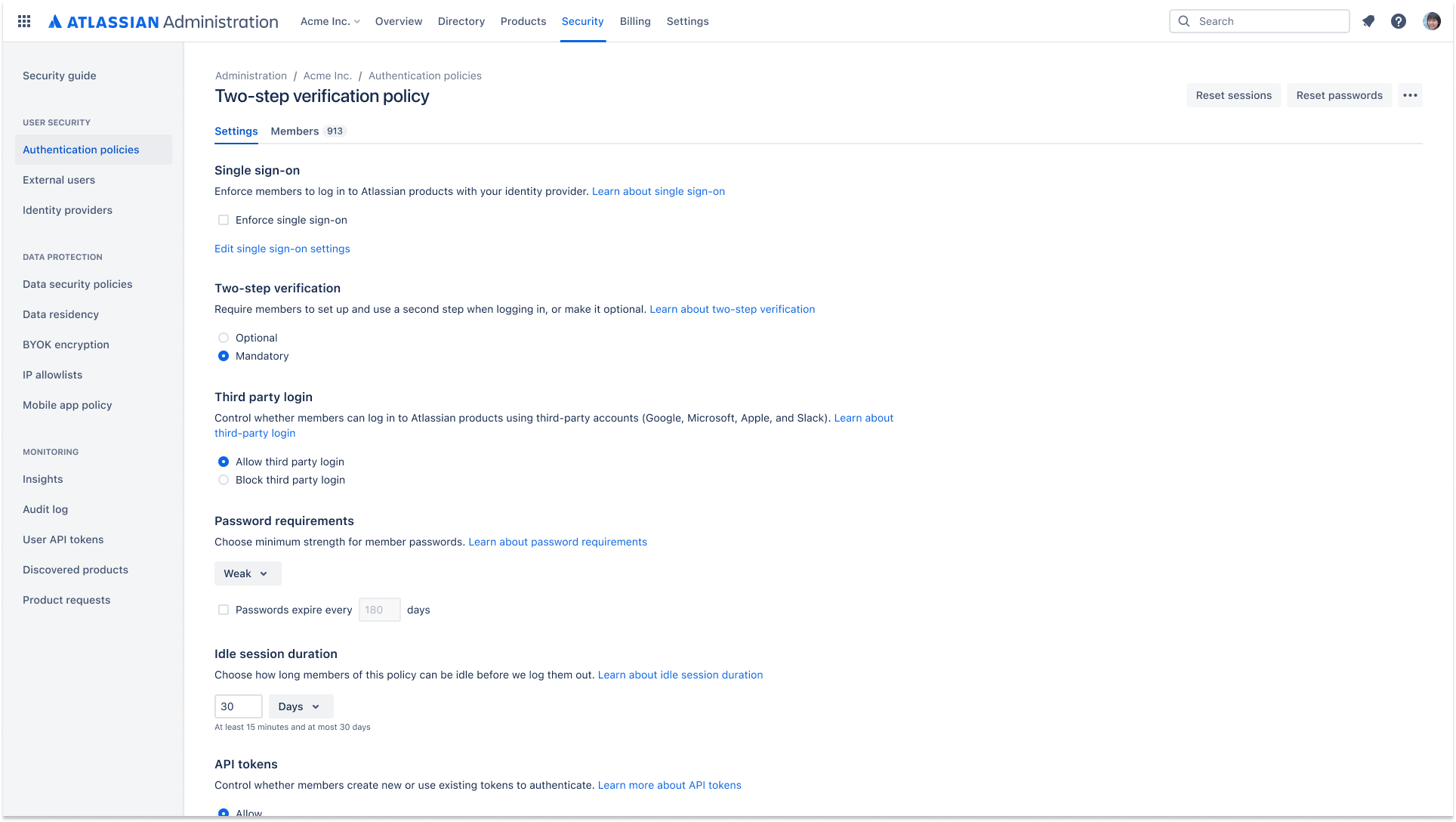
Enforced two-step verification can be applied as part of an authentication policy. This requires the users in an organization to turn on two-step verification in order to log in and access their Atlassian cloud products.